Version 1.0.0
It conceals your location and other personal data that are exposed when using standard browsers. Tor routes data through at least three servers, and websites will only see the IP address of the last server, not yours. It has features to maximize your privacy, unlike standard web browsers that have less stringent privacy protections. However, using Tor has some challenges that you should be prepared for.
Types Of Dark Web Sites (and What Really Goes On There)
The above mechanism conceals your location and browsing activities from third parties like internet service providers (ISPs), advertisers, and web monitoring apps. Data can still be exposed if you log in to certain sites or download files over the network. It’s an overlay network that enables encrypted, anonymous connections between computers. This protocol, a layer built atop the traditional internet layer, routes communication between random servers (called nodes or relays) to obscure the source. These servers, numbering in the thousands, are operated by volunteers worldwide. It doesn’t track your data, protects your identity, and is used via the Tor network.
Examples Of Security Theater And How To Spot Them
Also, the final relay of the Tor network is not encrypted, meaning that traffic between the exit node and destination server could be monitored. Toorgle allows users to discover hidden websites on the Tor network without necessarily requiring the Tor dark web browser itself. Functioning as a proxy, the Toorgle search engine crawls “.onion” links and presents text-based content and torrent files directly through its own interface.
A successful verification confirms the authenticity and integrity of the software, providing a critical layer of protection against potentially malicious versions. Deep Search is an open-source dark web search engine designed to index and explore onion space, the hidden services within the Tor network. Known for its accuracy, Deep Search stands out by delivering precise and useful results, avoiding the spammy links commonly found on similar platforms. Once connected to Tor, you’re ready to begin exploring the dark web. However, keep in mind that the dark web is not organized like the regular internet. Instead of search engines, you’ll need to rely on directories or specific .onion links.
How To Use The Tor Browser On MacOS And Windows
- This guide will cover the top dark web browsers, how they work, and the security benefits they offer.
- Originally developed to protect U.S. intelligence communications online, Tor is now used by the public for a wide range of purposes, both legal and illegal.
- First, you should know a little more about what you could be getting into.
- In some countries, evading government restrictions to seek new political ideologies is punishable.
I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Well, VPN over Tor is basically its opposite – instead of going through the VPN first, the signal passes through the Tor network, before going through the VPN.
How Does Tor Browser Work?
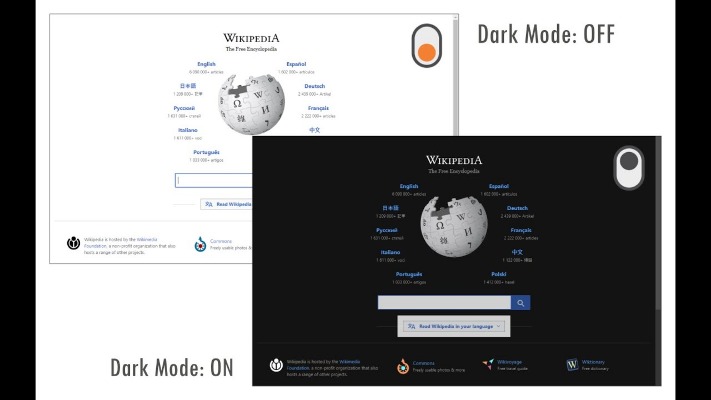
For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
- Therefore, the dark web should not be considered synonymous with the entirety of the unindexed internet; rather, it is a specific, intentionally hidden segment prioritizing anonymity and privacy.
- Traffic is relayed three times through random servers (or relays) as it passes the entry node, a randomized relay node, and a randomized exit node.
- Surfshark supports unlimited simultaneous connections to protect as many devices as possible.
- This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities.
- Services like Random Chat connects you with random people using the same service.
Getting Started: Downloading And Installing Tor Browser
Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. You can use a VPN if you’re in a country that restricts or heavily monitors Tor usage. You can also use it if you don’t want your network administrator or ISP to be aware of your Tor usage. However, if you don’t fall into these categories, or are a high-risk internet user (e.g., an investigative journalist or whistleblower), combining a VPN with Tor might be unnecessary. You can also use DuckDuckGo to find onion sites across the Tor network. To maximize security, you should avoid logging into personal accounts, such as Facebook and Gmail, via Tor.
Related Content

Subgraph OS uses Kernel hardening, Metaproxy, Sandboxing, Package security, Application network policies, Binary integrity, and Filesystem encryption to build robust security to their network. This is especially perfect for people in countries with tight internet control and surveillance. TAILS is a live OS that runs off a USB stick or DVD and leaves no trace.
Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. Formerly known as Archive.is, it is one of the best onion sites on the dark web.
While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network. Tor (The Onion Router) is a free and open-source dark web browser that enables anonymous communication by routing Internet traffic through a volunteer network of over 6,000 relays. The Tor Browser opens access to “.onion” sites, unique addresses within the dark web.
Unlike the surface web, where search engines like Google and Bing index vast amounts of content, onion services are generally not indexed by traditional search engines. This is partly due to their ephemeral nature and the privacy-centric design of the Tor network. As a result, users often rely on specialized search engines specifically designed to discover onion services. Examples of such search engines include DuckDuckGo (which also offers an onion service for privacy-enhanced searching), Ahmia, Torch, and DarkSearch. Tor is a browser built to help you anonymize your web activity and stay private online.
Governments worldwide have intensified online surveillance in the name of national security, while corporations increasingly monetize personal data. As digital rights erode, anonymity online is becoming a necessity rather than a luxury for many individuals. In your browser settings (like the NoScript extension in Tor), you will want to disable JavaScript and other active scripts.
Combined with the browser, it will provide maximum security and anonymity online. A VPN routes your online traffic through secure and encrypted servers to ensure you stay anonymous, unseen, and untraceable. It does this through high-level and top-quality encryption, providing you with an extra layer of protection at all times. The dark web consists of websites that have hidden IP addresses and use encryption software to keep their locations and users anonymous. Likewise, data can be transferred anonymously, making the dark web perfect for nefarious activity, such as drug transactions, gambling, pornography, and illegal firearm purchases. It’s a very dangerous place full of criminal activity and unsavory types.
It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code.



