
By using Forest VPN, you ensure that your internet service provider (ISP) and other potential eavesdroppers cannot trace your online activity back to you. Discover how to safely access dark web marketplace links while ensuring your privacy and security online. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. It allows vendors to sell without registration, which provides an added layer of anonymity, making it one of the more flexible and user-friendly markets on the dark web. The key differences between dark web markets and regular online stores are clear. Regular stores are public, with visible ads and a standard payment process.
Emerging Darknet Marketplaces Of 2025 Anatomy Tactics & Trends
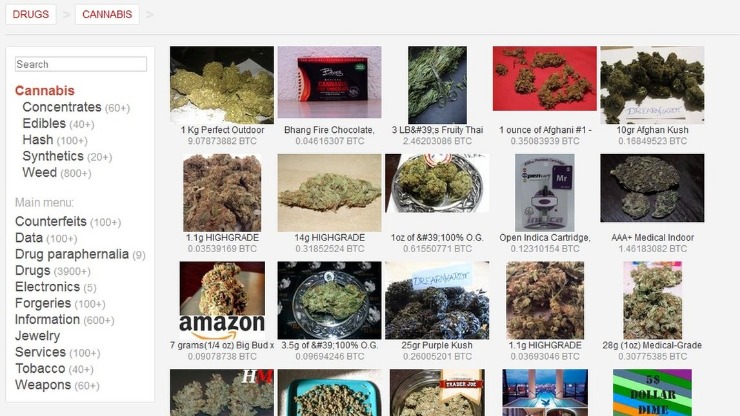
The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses. The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity.
Trusted Directories And Forums (stay Away From Hidden Wiki)
Our multi-layered approach ensures that every aspect of your interaction with our platform remains secure, private, and protected from potential threats. These official Black Ops Market onion links provide secure access to our Monero-only darknet marketplace. Always use Tor browser with JavaScript disabled for maximum security. Torzon market made its debut in September 2022, and ever since, it has been on an upward trajectory. In fact, it now features more than 11,600 illegal items, which include hacking tools, hard drugs, and all types of cybercrime services.
The Full List Of Trusted Darknet Markets:
Because of the range of goods and services found for sale and the conversations that occur around these sales, dark web marketplaces can be precious sources of data on criminal activity. As such, they are normally under intense scrutiny from law enforcement and security professionals alike. The most common darknet software is the free and open-source Tor, short for the Onion Router. The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs).
- I’ve used it a handful of times; deliveries landed smooth via DeadDrops—plain packaging, no fuss.
- When most people refer to the dark web, they are thinking about dark web/darknet marketplaces (DNMs).
- They also include user reviews and ratings, helping newcomers identify trustworthy vendors and avoid scams.
- It aims to expose abuses of power and betrayal of public trust through investigative journalism.
- Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero.
It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Unlike surface web platforms, darknet markets have no reliable way to verify vendors.
Markets List
An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions. Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations. The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes. Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty. Transactions within these marketplaces typically leverage cryptocurrencies—most commonly Monero, Bitcoin, and privacy-centric digital currencies developed specifically to enhance transaction anonymity.
How To Avoid Phishing Scams And Malware Threats
In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. Moreover, it’s not only the entertainment industry that gets hit; some sell cracked versions of the most expensive software, and others offer pirated eBooks and academic material at cheap prices.
Security Blogs
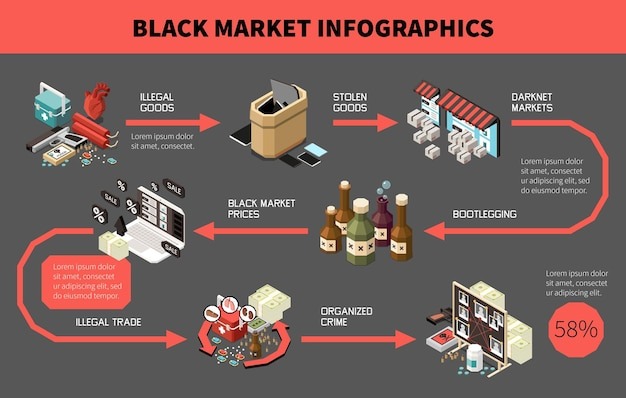
Dark markets are online platforms on the darknet where illegal goods and services are traded. You can find drugs, weapons, stolen data, and counterfeit documents on these marketplaces. They operate similarly to regular e-commerce sites but use cryptocurrencies for transactions.
- Vendors stake their craft—650€ in XMR cracks the gate—binding its pulse with every stash they seal.
- It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with.
- These platforms leverage advanced encryption technologies and decentralized systems to ensure transactions remain private and secure.
- Look no further if you want good music while navigating the dark web.
Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.

Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project.
Is The Dark Web Illegal?
It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. While there are many sites that facilitate illegal activities, there are also legitimate sites that provide valuable resources, including educational materials and tools for privacy protection. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons.
Look no further if you want good music while navigating the dark web. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability.
The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. Darknet marketplaces may look like regular online stores, but using or even browsing them comes with serious risks. From identity theft to law enforcement surveillance, the dangers are real — and often underestimated. The most secure darknet marketplace with advanced PGP encryption, multi-signature escrow, and anonymous Monero transactions. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it.



