And since fewer people were investing in cryptocurrency, there were fewer new accounts to hack. The internet itself started out as a private network before becoming publicly available. In that sense, the history of the Deep Web is as old as the history of the internet.
Bonus: The Silk Road
Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity. It has a search option to let you find local and international products and services on the dark web. A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment.
Dark Web Search Engine
This is also reflected in a study, according to which the distribution of stolen data increased elevenfold between 2015 and 2021. Due to its high level of anonymity, the darknet enables this data to be traded undetected, making it easier for criminals to conceal their identity and evade prosecution. In addition, the use of cryptocurrencies facilitates anonymous transactions, which further simplifies the trade in stolen data. At the same time, the professionalization of darknet markets has led to a safer and more efficient trading environment. These markets offer user-friendly interfaces and reliable services, further fueling the trade in stolen data. Finally, the growing demand for stolen data used for illegal activities such as identity theft, fraud and phishing is helping to strengthen the market.
Explore The Products
One of the central76 discussion forums was Reddit’s /r/DarkNetMarkets/,777879 which has been the subject of legal investigation, as well as the Tor-based discussion forum, The Hub. Each marketplace is a star-graph where the central node is the marketplace, and the leaf nodes, i.e., the first-neighbors, are the marketplace users. Therefore, all transactions involving the market have the market either as a source or as a destination node. To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13.
VPN Alternatives For Securing Remote Network Access
Internet Relay Chat (IRC) was once the nerve centre of early cybercrime. Groups used password-protected channels to trade exploits, stolen data, and malware kits. But as operations scaled, IRC’s static architecture and lack of mobile adoption left it vulnerable. The torch passed to dedicated darknet forums, often on the Tor network, which allowed marketplaces and vendor reputation systems to emerge. Its mobile-first design, ease of channel creation, and semi-anonymous architecture made it an attractive choice for actors who needed speed and reach more than secrecy. In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
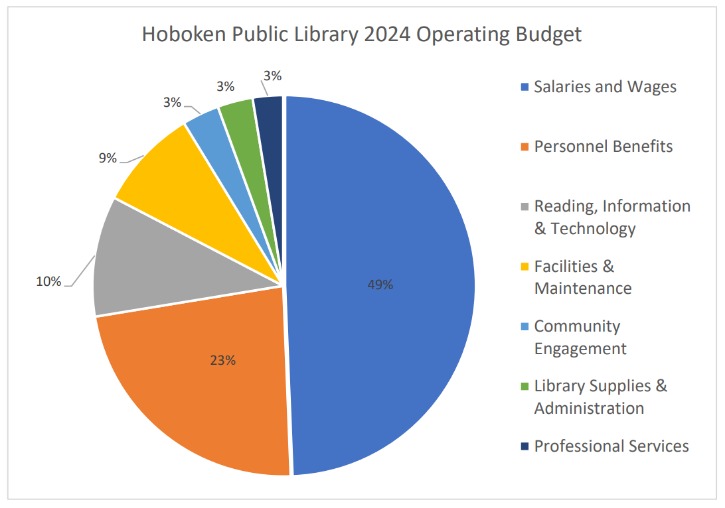
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse. The number of dark web listings that could harm an enterprise has risen by 20% from 2016 to 2019. Of all listings (excluding those selling drugs), 60% could potentially harm enterprises. U.S.-based drug vendors on Abacus Market advertising a synthetic opioid called China White, which its customers can purchase using Bitcoin or Monero. The chart above shows that ASAP and Mega Darknet markets led the large retail and wholesale segments respectively.
For instance, we cannot verify if an entity classified as seller is in fact a seller. Similarly, there is no unique choice for the classification parameters or ground truth for fitting them. In light of this, we have chosen the parameters conservatively, obtaining estimates for the number of sellers that are in general smaller than the ones produced by other methods. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks.
One China-based pill press manufacturer which advertises on clearnet business-to-business (B2B) websites has on-chain ties to drug vendors on Abacus Market. Along with its listings for large pill press machines, the vendor does not hide the sale of Oxycontin and Xanax TDP die kits, which are used to press counterfeit pills. The vendor accepts BTC and XMR, and analyzing its on-chain exposure to regional CEXs and DNMs reveals that it serves customers worldwide, including in the United States, Canada, Sweden, and Russia. The Reactor graph below shows this vendor’s connection with drug vendors on Abacus Market.

Which Is The Best Laptop For Cyber Security Course?
- Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases.
- It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.
- The markets often share materials related to child exploitation, pornography, and non-consensual recordings, all of which are serious crimes that inflict lasting harm on real-life victims.
- In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
- This project aims to preserve darknet market data for research, intelligence gathering, and historical reference.
Such uses prove how the dark web can serve important social functions. Fill out the form to speak with our team about investigative professional services. You can see if your email address has been exposed in a data breach without creating an account. However, to receive alerts when a new data breach occurs and a detailed report, you’ll need to create a subscription account. Yes, many professionals use tools like Maltego, IntelX, and custom scripts to automate scraping, indexing, and alerting on dark web activity.
DrugHub Market
ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live. The good news is that the BBC Onion site is an international edition.
Darknet Market Vendors Evolve Their On-chain Behavior
Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. Rating services are increasingly popular since dark web marketplace “exit scams” remain high. There is no honor among thieves in many corners of today’s dark web. “Exit scams” occur when marketplace operators suddenly shut down, stealing funds from escrow wallets and disappearing.
The many ways in which stolen data can be misused are complex and do not end here. Prior to its takedown by law enforcement, narcotics traffickers and cybercriminals openly traded in illegal drugs and services on Nemesis, which was designed with built-in money laundering features. Nemesis had over 30,000 active users and 1,000 vendors and facilitated the sale of nearly $30 million worth of drugs around the world between 2021 and 2024, including to the United States. Today’s sanctions designation is OFAC’s first action as a member of the Federal Bureau of Investigation (FBI)-led interagency Joint Criminal Opioid and Darknet Enforcement (JCODE) Team. The expansion of data trading can be attributed to several factors. The increase in data breaches and data leaks has led to more personal data being available for trading on the darknet.
Its user base is primarily English-speaking, and it appeals to more sophisticated cybercriminals. Over the years, dozens of large DNMs have been established and eventually shut down by law enforcement, including AlphaBay, Dream Market, Wall Street, and, most recently, Hydra. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed.
As reported last year, some drug shops have been outsourcing services like website hosting and payment processing. IKlad.biz and Klad.cc, shown in the chart above, are examples of those infrastructure providers. While these outfits are not traditional DNMs, their success highlights how drug vendors are scaling their operations throughout Russian-speaking countries. In spite of Hydra Market’s disruption in 2022, former Hydra affiliates still found operating in today’s DNMs rely heavily on these infrastructure providers. Last December, a Russian court imposed a life sentence on Stanislav Moiseyev, Hydra Market’s suspected founder and operator, although the Moscow prosecutor’s office did not publicly tie the guilty verdict to Hydra. The court also sentenced fifteen accomplices to anywhere from eight to 23 years in maximum-security penal colonies.



