While it’s not a browser, it includes Tor Browser installed by default that provides anonymity for web browsing and enables users to access the dark web. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow.
Protect Yourself Against Tracking, Surveillance, And Censorship
However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
- On the other hand, if Whonix sounds like too much, you can opt for the Tor Browser Bundle for the default dark web browsing experience.
- One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
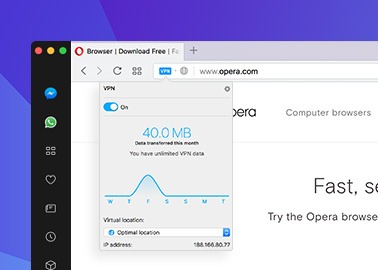
- And even if you find a VPN that does, you’ll still need to perform a manual setup, which is inconvenient and time-consuming.
- Tor is a network designed to route traffic through multiple servers.
- As a result, it not only focuses on the UK but also provides worldwide news.
- Governments worldwide have intensified online surveillance in the name of national security, while corporations increasingly monetize personal data.
It’s designed for secure, decentralized storage and is often used for file sharing and accessing information anonymously. While Tor is the most common method for accessing the dark web, I2P and Hyphanet offer alternative options for secure and private browsing. Let’s go through the setup process for each, as well as how to use them effectively. If you want to improve your security further, you could also use a VPN at the same time as Tor. For the most security-conscious, you can even install the Tails operating system on a flash drive and run Tor from that.
You’ll find the more dangerous content and activity at the dark end of the deep web. This is where Tor websites are located, deemed the ‘dark web,’ and can only be accessed by an anonymous browser. For this reason, users should be cautious when using their browsers. The dark web is a hidden part of the internet that can be accessed through limited resources.
The Role Of Forest VPN
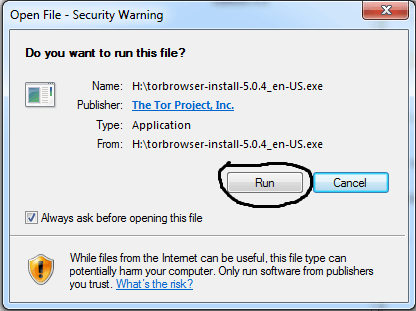
There are four nodes between your computer and the website you want to connect to. The browser uses a unique security system, which the United States Navy originally developed to protect the government’s intelligence communications. The browser is available for Linux, macOS, and Windows desktop and laptop computers.
The Hidden Wiki & Co

The exit node can also be compromised but our experience has shown this happens extremely rarely. Besides, if the exit node malfunctions, you still have your trustworthy VPN so no one can track your footsteps. If you don’t know where to start, you can use The Hidden Wiki to find a few dark web domains. Simply copy the URL of the site you want to visit, press Enter, and you’re all set. The button above leads you to its website where you can claim an exclusive 70% discount for the 2-year plan. Click the button, get the provider for around $3.3/mo, and install it on your device.
Best WiFi Security Protocols: Which One Should You
Below is a comparative analysis highlighting key criteria such as connection speed, level of anonymity, ease of use, and support quality for the top options available in 2025. The dark web remains one of the internet’s most intriguing yet misunderstood environments. Tor has an in-build slider which lets you adjust the level of security. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman.
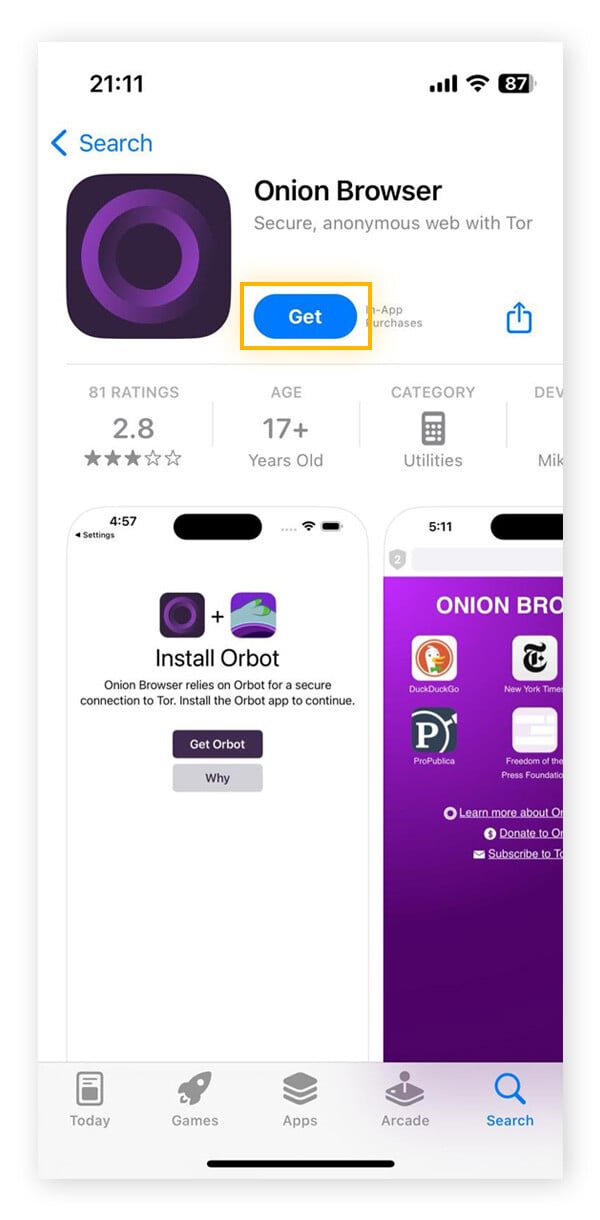
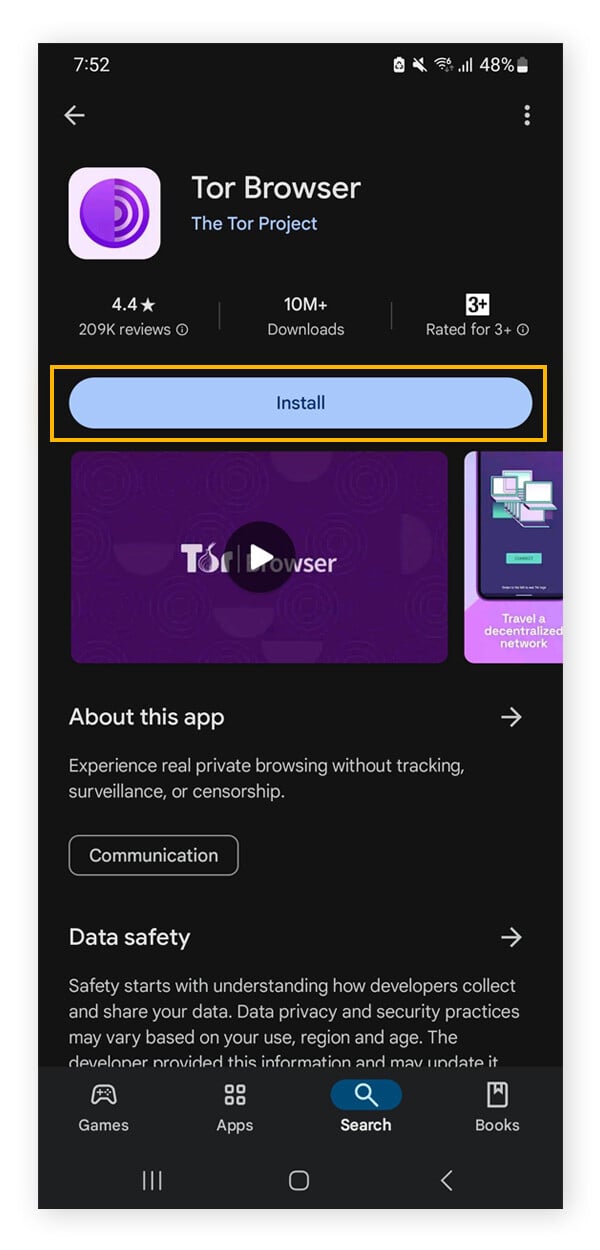
How To Download And Use Tor
In an onion network, messages are encased in layers of encryption, much like the layers of an onion. The encrypted data is sent through a series of network-based nodes called onion routers. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting. The Tor Browser is a popular online anonymity tool among political activists and journalists who fear totalitarian governments monitoring or arresting them. Other users appreciate the browser as it allows them to circumvent censorship.
Remember only to make purchases using digital currencies and never provide any online banking login details. You’ll know you’re on the dark web when the URLs end in “.onion” — these addresses only work inside the Tor network. The dark web is a small portion of the deep web that has been intentionally hidden and is inaccessible through standard web browsers. To access it, you need dark web browsers like Tor, which allows users to browse anonymously by bouncing their connections through a global network of volunteer servers. Staying off the dark web, if possible, is crucial for several reasons, primarily due to the inherent risks and illegal activities that dominate this hidden part of the internet.
Navigating The Shadows: Accessing Onion Services
However, even these resources are not immune to compromise or the inclusion of malicious links, so a degree of skepticism is always warranted. Finally, users whose internet connection relies on a proxy server can configure these settings within the “Configure Connection” window as well. This typically involves entering the proxy type, address, and port, and potentially authentication details if required by the proxy server. In most home network setups, proxy configuration within Tor Browser is not necessary, as the browser is designed to route traffic through the Tor network independently. That doesn’t mean it’s impossible to track users on the dark web.
What’s more alarming is the estimation that the HALF of those visitors were connected to illicit activities. We can conclude that this portion of the internet can be dangerous but again, you’re in control and decide which websites you want to visit. PIA is popular in the USA because it offers servers in all 51 states. People in the United States and abroad can use it to venture into the dark web in privacy. With RAM-based servers in 90+ countries and features like WireGuard, IPv6 leak protection, and a kill switch, worries are over.
Drugs are typically sold using cryptocurrency to maintain anonymity, and the buyers and sellers are often difficult to trace. These markets operate similarly to physical drug markets but are hidden from law enforcement through the use of the Tor network. Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information.
Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface. If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages. So, you’ll be happy to know there are several easy ways to delete a page in Word, including both blank pages and those you simply no longer need. Dark web marketplaces offer a range of both legal and illicit goods. Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023. By monitoring known dark web marketplaces, Avast BreachGuard will alert you immediately if and when your data is found.
Instead, I2P uses its own brand of hidden sites called “eepsites”. Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed. Avoid fraudulent Tor-like browsers that compromise your online security.



