The Onion Project, or TOR is the predominant anonymous computer network. It works kind of like a VPN, but instead of routing your traffic through one remote server, it routes it through many random servers across the globe. The Silk Road dark web marketplace changed the way cybercrime operates, showing how technology like Tor and Bitcoin can facilitate anonymous transactions. Although Silk Road was shut down, it marked the beginning of a new era of cybercrime, inspiring countless similar operations and underscoring the role of technology in modern crime.
Typical Use-Cases Of Dark-Web Marketplaces In 2025
It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero. Another dark net marketplace that has grabbed a lot of attention is the Hydra market. The entire website is in Russian, but the vendors are present worldwide.

Illegal Markets
The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. This website is made public with the intention to aid the Internet users with navigation of the so called dark web. We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor. These domain names are not registered with a central authority but are instead derived from cryptographic keys.
Never Use Your Credit And Debit Card For Purchases
With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns. Later, in 2013, Silk Road caught the attention of law enforcement and policymakers like US Senator Charles Schumer, who publicly called for a federal crackdown.
FAQ: More About Onion Sites
We’ll explore their unique features, common use-cases—both legitimate and illicit—and the significant risks users face when interacting with these platforms. The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency. The marketing and sale of illicit substances occurs on the surface web, encrypted and non-encrypted chat platforms, via social media direct messages, in addition to the darknet. Online purchases of drugs are often delivered to a mailbox or a “dead drop” location, or sellers utilize mail services or international trade networks. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet.
Use Cryptocurrency For Transactions
However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked.

As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
Is The Dark Web Illegal?
This browser is the most suitable option for accessing the dark web, thanks to its multiple layers of encryption. Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. DuckDuckGo is a helpful search engine available on the Tor that allows you to browse the dark and regular web anonymously. mark it means it has been verified as a scam service and it should be avoided. If the website you are trying to visit has Recommended mark it means it has been verified and is safe to use. As stated above, we don’t condone any activity—on the dark net or otherwise—that is forbidden by law.}
Home Products
Combining robust encryption, flexible payment options, and responsive support, Vortex is engineered for those who value both efficiency and anonymity. TorZon is a well-known name in the darknet landscape, recognized for its streamlined marketplace experience and long-standing presence in the community. Since its emergence, TorZon has focused on providing a secure and anonymous environment for users seeking privacy and stability. With a clean interface, reliable uptime, and active vendor support, it continues to stand out as a trusted hub for darknet commerce. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.
Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. Other sites explicitly block search engines from identifying them.
- You can find items like digital goods, software, and even collectibles.
- Several papers have uncovered essential phenomena related to DWMs.
- This hides your activity and personal identifiers so you can browse safely, protected from prying eyes and identity theft.
- It allows access to the .onion sites on the dark web that you won’t find using a regular browser.
Accessing DNMs
- George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years.
- The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now).
- Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
- Finding a trusted dark web marketplace can be difficult, but we offer everything users need for a safe and smooth experience.
By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero. Fresh Tools Market has become a go-to platform for cybercriminals seeking access to malicious software such as keyloggers, Remote Access Trojans (RATs), and ransomware-as-a-service. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Launched in 2021, Abacus Market caters primarily to English-speaking users. Further market diversification occurred in 2015, as did further developments around escrow and decentralization. Still, the existence of this content is a grim reminder of the dark web’s potential for abuse when left unchecked.
The Daniel site also had a status check feature that updated users on which sites were active. Unfortunately, the site’s admin could not keep up with the time demands and has taken down the links on the site as of August 2023. Onion sites are far safer to use as they are hidden deep within the deep web. Also, since users can only access them using the Tor browser (with its high-end encryption), users can be rest assured their identities and locations remain hidden. Cybersecurity tools like CybelAngel’s external attack management (EASM) platform can help businesses monitor the dark web effectively.
While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information. This trove of stolen data included names, addresses, Social Security numbers, and phone numbers, leaving millions of individuals vulnerable to identity theft. Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps.
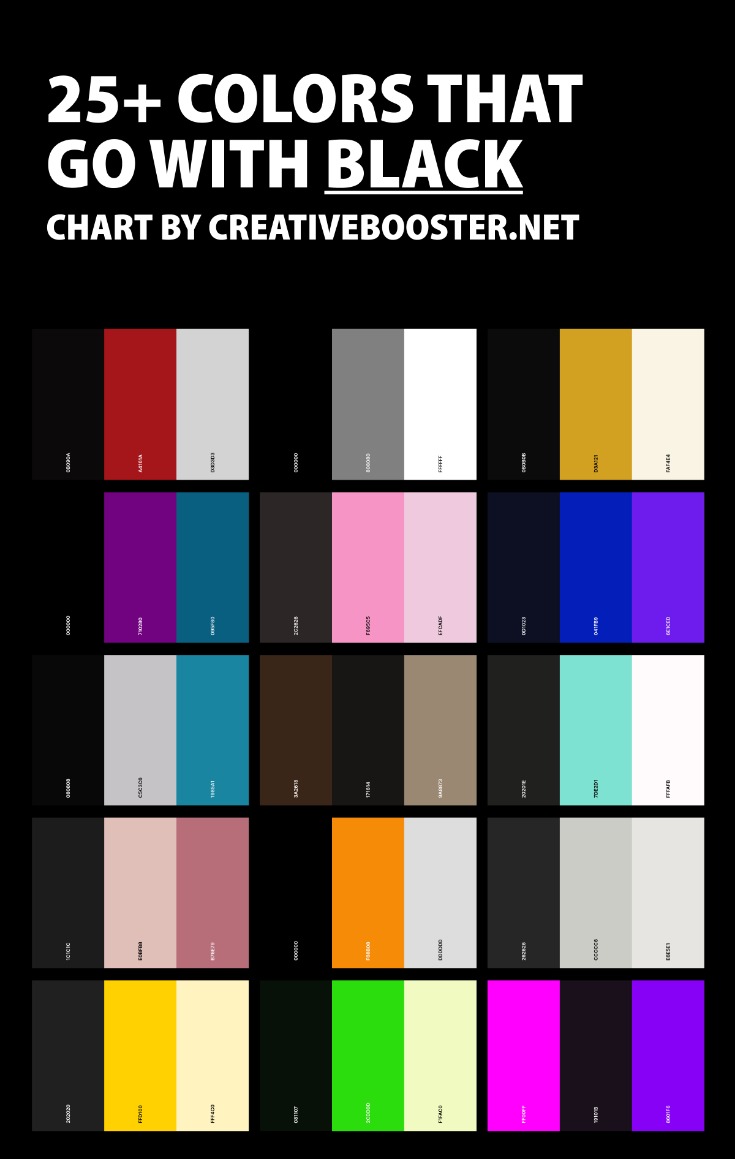
In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses. Dark web marketplaces are websites where you can exchange illicit goods and services like stolen credit cards, account login credentials, counterfeit items, drugs, and other items. Usually dark web transactions are made with Bitcoin or other cryptocurrencies. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.



