
Instead, you\’ll need to independently seek out the specific dark websites you wish to explore. This unique browsing experience underscores the user\’s active role in navigating the intricacies of the Dark Web landscape. Malware, ransomware, and hacking tools are also readily available for purchase or rent, enabling attackers to launch sophisticated campaigns. Additionally, forums facilitate the exchange of exploit kits and zero-day vulnerabilities, which can be weaponized before patches are released. The anonymity of the dark web makes it a fertile ground for coordinating cyberattacks and sharing illicit services without detection.
Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Open up Tor, and you won’t suddenly see the dark web staring back at you. Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs.
Take Extra Security Precautions
However, this feature is only available on iOS, Android, and Windows. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously.
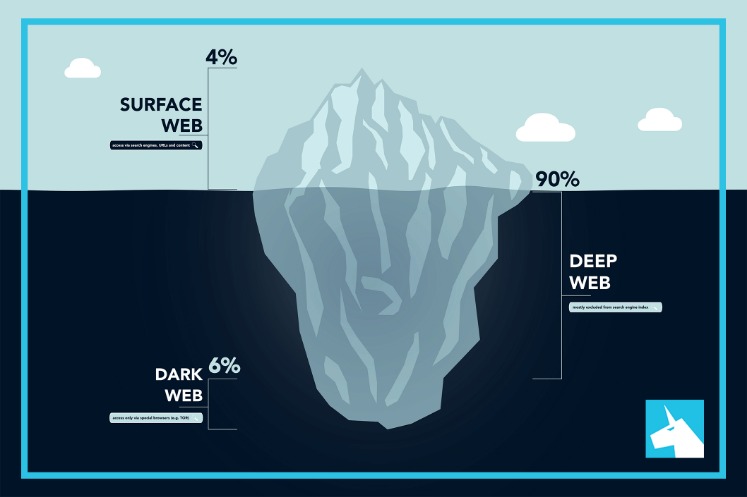
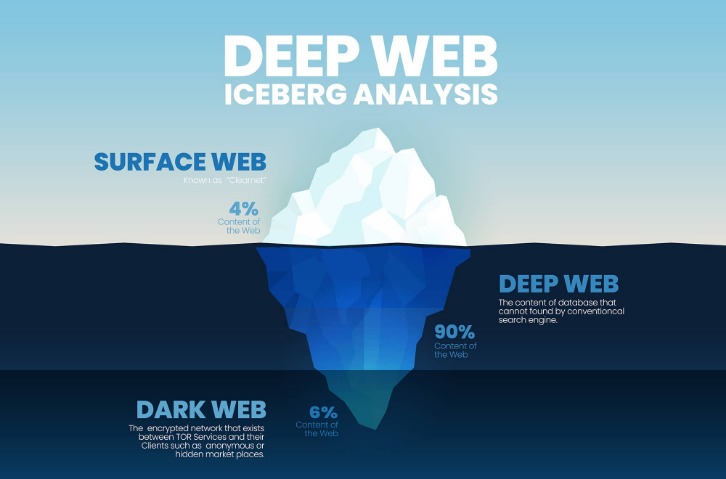
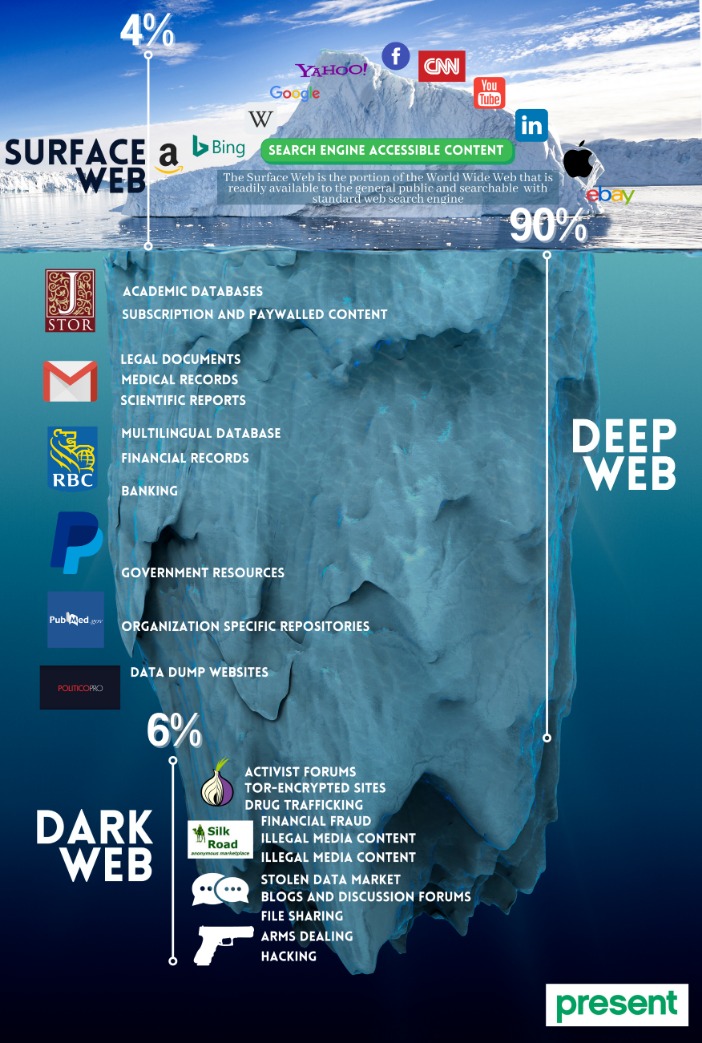
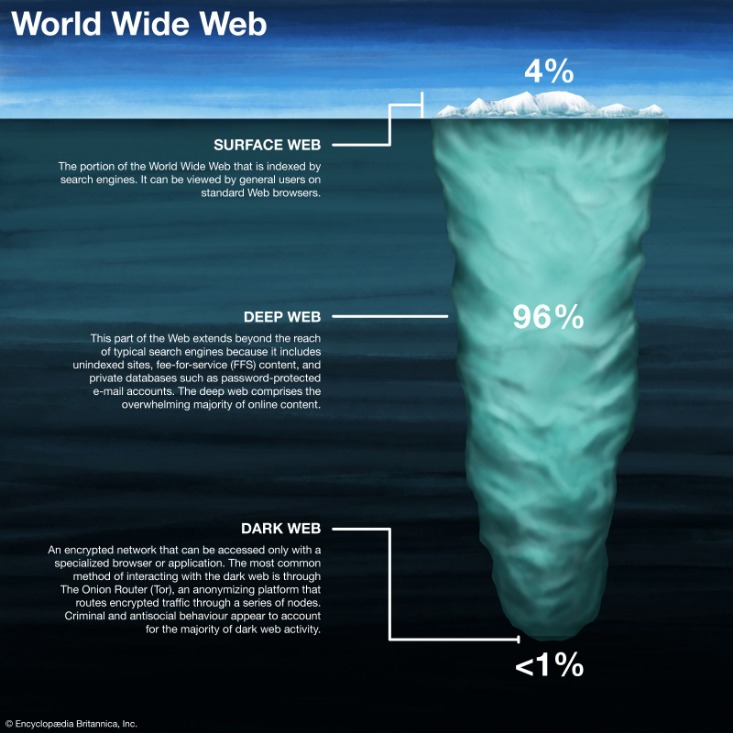
They rely on it for anonymous, secure communication to avoid surveillance or censorship. It also helps users bypass government restrictions to access censored information and services. No — the deep web includes any online content that isn’t indexed by search engines, like your email inbox, banking pages, or private databases. The dark web is a small part of the deep web that’s intentionally hidden and can only be accessed through special browsers like Tor.
For additional protection, enterprises should monitor the dark web to identify indicators of dark web compromise, such as database dumps or the posting of personal or financial information. Regular monitoring can provide early alerts of possible threats, which can facilitate prompt responses to mitigate the potential effects. Organizations can also consider dark web monitoring services that search through data available on the dark web for anything related to their specific company or employees. Dark web monitoring can supplement other tools used to gather preemptive threat intelligence, such as the Mitre ATT&CK framework. Indexes of website links allow Google and other search engines to return relevant results whenever a user types a keyword into the search bar.

How To Find Out If Your Information Is On The Dark Web
You can sort search results by age, set your location manually, and adjust safe search settings. It’s one of the best choices if you want a familiar and private search experience on the internet. China, for example, blocks access to the Tor network entirely, treating it as a tool for bypassing government controls.
Marketplaces For Everything Illegal
Venturing further into the deep web does bring a bit more danger to the light. For some users, portions of the deep web offer the opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas. Others go somewhat deeper to download pirated music or steal movies that aren’t yet in theaters.
Onion Links: How To Access Them
From a statistical standpoint, this collective of websites and data makes up under 5% of the total internet. The U.S. has a strong legal framework when it comes to cybercrime, and many of those laws apply directly to activity on the dark web. While the dark web itself isn’t illegal, several laws come into play depending on what’s being done. Choosing a dark web monitoring tool requires a lot of factors, including price, availability, and many other things.
- A repository of sites that can’t be found by traditional search engines, the dark web is as intriguing as it is dangerous.
- The internet providers and websites can still see that you’re using Tor as Tor node IPs are public.
- Since then, the dot-com boom became the dot-com bubble, technology fundamentally altered our lives, and everything has become about security.
- The platform is also used by governmental cyber departments to identify and track potential criminals or offenders.
- It aimed to provide online privacy by routing internet traffic with a series of volunteer-operated servers, encrypting the data at each step, and making it challenging to trace the user’s identity.
- Journalists, whistleblowers, and researchers often use it to protect their privacy or gather sensitive information.
Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser. Also, you can set a strong password to protect your message and choose how long it will take to expire. While this is not much compared to standard email services, it is enough for PGP-encrypted messages.
What To Do If You See Something Illegal
First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web. However, remaining anonymous can be invaluable to protesters, civil rights groups, journalists, lawyers, and other vulnerable groups.
What Are Ransomware Leak Sites
Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. A VPN will mask your location and stop the online breadcrumbs that can lead back to you. Connections made while a VPN is active will also be encrypted, helping you stay protected from eavesdropping and man-in-the-middle attacks. You can usually select the location you want to appear to originate from and VPNs will use a collection of servers and relays to make tracing your IP difficult.
Recognizing Common Scams And Deceptive Tactics
Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites. But of course, these benefits can be easily extended to those that want to act outside of the constraints of laws in other explicitly illegal ways. That said, a significant chunk of U.S.-based activity on the dark web still revolves around illegal marketplaces—selling things like stolen data, counterfeit documents, and even drugs. Staying cautious is essential when interacting with content on the dark web, as illegal activities are prevalent.
Many transactions conducted on the Dark Web involve the exchange of cryptocurrencies, as they offer a level of anonymity that traditional currencies cannot. The most notorious marketplace to date was Silk Road, an online black market for drugs, which was shut down by the FBI in 2013. Despite this, similar markets have continued to emerge, fueling the Dark Web’s reputation as a haven for illegal trade.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.



