Most likely, the native account on your device has full admin permissions by default. Therefore, you can prevent this exploitation by setting up a non-admin account. Also, use an effective antivirus program to check threats if you decide to download files. You can check out this guide on the best antivirus software applications today. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
How To Delete Yahoo Account In 2025
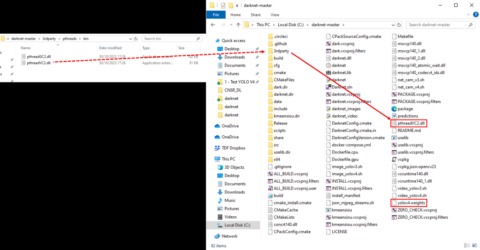
Accessing the dark web can only be done using specific browsers, such as TOR Browser. I always cross-reference links from multiple verified sources before visiting any dark web address. A reliable VPN encrypts your traffic before it enters the Tor network, preventing surveillance from your ISP or malicious actors.
Sites on the dark web typically use .onion domain names, which add a layer of anonymity for both users and administrators. While many users turn to the dark web for legitimate reasons, such as journalists or activists seeking to avoid censorship, it is also known for illegal activities. It also sells VPN and initial access, a marketplace, making Exploits.in the favorite dark web forum for ransomware hackers.
Can I Report Suspected Darknet Activity?

Pitch is a dark web-based Twitter/X alternative, providing a secure platform for anonymous discussions and information sharing. Unlike many dark web platforms, it maintains strict content guidelines while protecting user privacy. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private.
Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. The dark web contains content that’s only accessible through networks like Tor.
Does The CIA Have An Onion Site?
A hacked Netflix 1-year subscription retails at $25; an HBO account is $4, a Bet365 account is $40, and a hacked Uber account will set a cybercriminal back $15. If you’re connected to a public WiFi network, avoid making any purchases online while you’re connected to the network as this could place your financial data at risk. These dangers can interrupt business operations, defraud a company and devalue a brand’s integrity.
Dark web and deep web forums expose the darker side of the internet, often hiding illicit activities from the public eye. These platforms provide cybercriminals with anonymity, making it difficult to track and stop illegal activities. While some users seek privacy, the ease of trading stolen data and illegal services remains a major cybersecurity concern. Darknet carding sites are hidden websites accessible through specific networks like Tor. They provide a space for cybercriminals to buy, sell, and trade stolen financial information, typically credit cards and personal identification data.
Dark Web Carding Forums
- It aims to expose abuses of power and betrayal of public trust through investigative journalism.
- Stolen credit card details can be categorized into different types, making it easier for cybercriminals to exploit them.
- We developed Lunar to monitor the deep and dark web, including dark web marketplace sites.
- It provides an .onion URL and an interface for you to manage your Tor site easily.
- Phishing schemers buy pre-made scam pages to convince users they’re visiting a legitimate website.
|}
The stolen credit card information sold on these sites can vary in quality and price. Some sites may sell “fullz,” which include the victim’s name, address, Social Security number, and other personal information, in addition to the credit card number and expiration date. Other sites may sell “dumps,” which are raw credit card data extracted from the magnetic strip of a physical card. Some card issuers offer identity protection to cardholders, and others offer it to anyone and everyone. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship.
The Tor Times
A network browser gives you access to sites with the ‘.onion’ registry operator. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. It works by sending internet traffic through volunteer-operated nodes all over the world.
Torzon Market
The cloak of anonymity provided by the Dark Web has led to its association with illicit activities and cybercrime. The term darknet carding sites refers to online platforms on the dark web where individuals can buy and sell stolen credit card information and other financial data. These sites operate under the radar, often requiring specific software like Tor to access, adding a layer of anonymity for users. Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web.
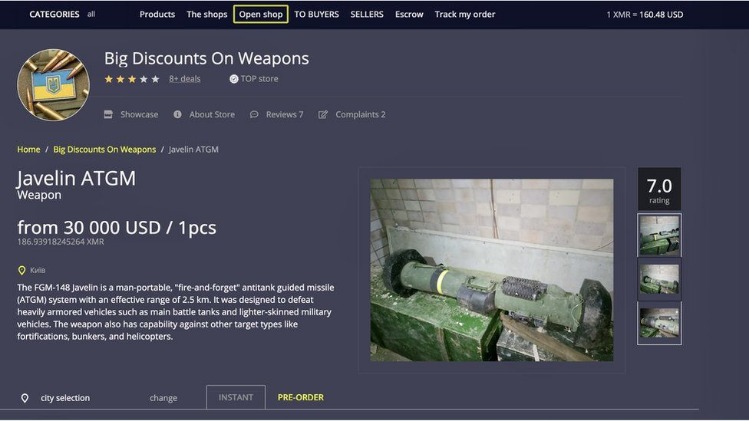
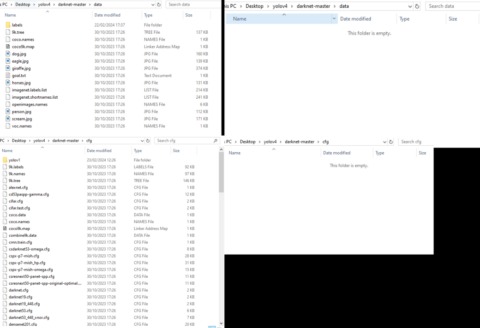
Darknet carding sites operate by allowing cybercriminals to sell stolen credit card information to buyers. Sellers typically obtain credit card information through phishing scams, data breaches, or by using malware to infect computers and steal information. Once they have obtained the credit card information, they sell it on darknet carding sites to buyers who are looking to commit fraud. Onion sites are used for a variety of purposes, but the common thread is privacy and anonymity, both for users and service providers. It is nearly impossible to trace the activity on onion sites, including the identities of people who use them. It’s a hidden collective of sites that you could only access through a special browser.

TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need.
Carders target sites without these protections, and some vendors even sell lists of “cardable” sites for a few dollars. Dark web posts and offers of this size are usually scams, so the massive dump of cards could easily be fake data or recycled data from old dumps repackaged under a new name. To ensure larger reach, the crooks distribute the collection via a clearnet domain and on other hacking and carding forums. Recovering stolen data is highly challenging, but contacting financial institutions immediately can help mitigate potential losses. Accessing the darknet typically requires special software like Tor, which anonymizes user activity.
Types Of Dark Web Sites (and What Really Goes On There)
- The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage.
- You need to ensure you’re only accessing reliable dark web sites, and the ones listed below are among the safest ones that currently work.
- The primary goal of these sites is to facilitate the sale and purchase of stolen financial information for illegal purposes, primarily fraud.
- It includes all the essential productivity software, including MS Word and an email client.
- For example, China uses the Great Firewall to block access to Western sites.
These sites offer a marketplace for cybercriminals to buy and sell sensitive financial data, often leading to significant financial losses for individuals and businesses. Buyers on darknet carding sites typically use the stolen credit card information to make purchases online or to create counterfeit credit cards. They may also use the information to commit identity theft or to sell the information to other cybercriminals. The buyers and sellers on these sites often use sophisticated methods to evade detection, such as using VPNs and anonymized payment methods. These measures include implementing robust security practices, such as encryption and multi-factor authentication, to protect credit card data and reduce the likelihood of it ending up on the dark web.
Some are geared towards academic, professional, or hobbyist communities, while others are havens for illegal activities. Here’s an overview of some of the most well-known dark web forums and deep web forums that have emerged over the years. While SSN, name, and DOB are all fairly standard in fullz, other information can be included or excluded and thereby change the price.



