What can really retain customers is the excellent user service and experience. DWM users display complex trading patterns within the marketplace environment. For example, users migrate to alternative DWMs when a DWM that they trade on closes12,13. Such migration of users is aided by communication via online forums and chats on the dark web14,15. However, little is known about how DWM users trade and transact outside the DWMs.
Legal Disclaimer
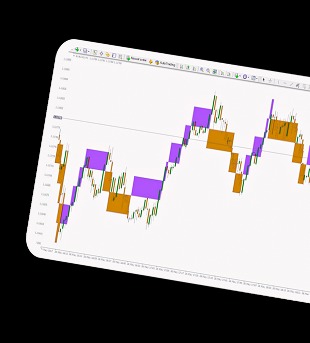
Recent results have shown that transaction networks and activity on DWMs and regulated online marketplaces share several robust macroscopic properties43. One might therefore hypothesise that U2U trading is also a prevalent feature on regulated online marketplaces. We have shown that the U2U network is resilient to abrupt external shocks, such as marketplace closures, and does not need the centralised structure of DWMs to survive. To answer this question, we consider the impact that the COVID-19 pandemic has had on the evolution of stable U2U pairs.
How Does Insider Trading Work On The Dark Web?
Changing the Tor browser settings can further boost your security levels on the dark web shops. For instance, you can choose the preferred security levels for enhanced protection. The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year.
What To Do If You See Something Illegal
This can have serious repercussions for investors, who may be unaware of the fraud until it is too late. RedOwl says that risk management teams need to actively build insider threat programs and not just focus on external threats to their systems and data. The company says that while 80 percent of security initiatives focus on perimeter defense, fewer than half of organizations spend anything at all on insider threat protection. All information on The Forex Geek website is for educational purposes only and is not intended to provide financial advice. Any statements about profits or income, expressed or implied, do not represent a guarantee. Your actual trading may result in losses as no trading system is guaranteed.
Strategies For Conducting Legal And Ethical Research On A Company

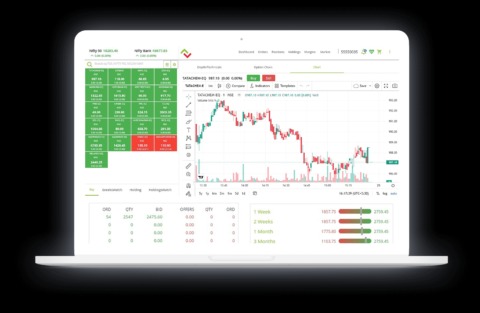
It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. The foreign exchange market, commonly known as Forex, is the largest and most liquid financial market in the world.
- Hacktivist obtained the user database of the website, enabling the FBI to trace the true identities of individuals.
- Sensitive information is protected via encryption against external monitoring and detection.
- If someone is offering you insider information or claiming to have access to such information, it is likely a scam.
- However, unlike the multiseller network, the S2S network recovers during 2019 and 2020, but slower than the multibuyer network recovery.
- Additionally, we observe that, except for U2U-only sellers, the median income of the other types of sellers drops after the major shock caused by operation Bayonet (see Supplementary Information Section S4).
- The Tor-based dark web uses this protocol to maintain the anonymity of dark web users.
Launched in 2021, Abacus Market caters primarily to English-speaking users. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. Many services that are allegedly offered on the dark web are scams.
Supporting Illegal Activities Unknowingly
The dark web, an enigmatic subset of the internet, operates as an encrypted and anonymous network inaccessible through standard web browsers. Unlike the surface web, which is indexed and easily searchable, or the deep web, which houses private databases and unindexed content, the dark web is a haven for covert activities. It facilitates a range of illicit trades, including the sale of stolen data, hacking tools, counterfeit documents, illegal drugs, and firearms. A dark web market is a hidden online platform where users can anonymously buy, sell, and trade illegal or sensitive items. Such markets are typically accessible through the Tor network, which anonymizes traffic by routing it through multiple relays and encrypting each layer. This encryption makes attribution and tracking more difficult for authorities and cybersecurity professionals.
Any legal analysis, legislative updates, or other content and links should not be construed as legal or professional advice or a substitute for such advice. If you require legal or professional advice, kindly contact an attorney or other suitable professional advisor. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks.
What’s Hot On Darknet Markets In 2025
Insider trading on the dark web has developed into well-organized networks from random, isolated incidents. To carry out insider trading operations on a bigger scale, criminal gangs with specific expertise, such hackers, financial analysts, and data brokers, have joined forces. These organizations take advantage of the dark web’s anonymity to plan their actions without worrying about being found out. Law enforcement agencies and international coalitions play a critical role in countering dark web activities.
This includes using an anonymous browser like Tor, a VPN to encrypt your connection, an antivirus for protection against malware (we recommend TotalAV), and generally being careful not to reveal personal information. Accessing Abacus Market involves a few essential steps to ensure your safety. Next, obtain a verified onion link from our list above, which are vetted to prevent phishing. Open the link in Tor, complete any CAPTCHA challenges, and proceed to the login page. If you’re a newcomer, register with an unlinked username and a strong password. For details, refer to the Access section for a comprehensive guide.
- These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going.
- The dark web, also known as the hidden web, is a hidden server contained in the “deep web”.
- The discussion forum must, first and foremost, be secure for all users.
- However, trading behaviour in DWM closely resembles what is observed on regulated online platforms despite their significant differences in operational and legal nature14.
- Law enforcers can use custom software to infiltrate the dark web and analyze activities.
Individuals can trade with such information, profiting illegally without a paper trail. The Securities Exchange Commission (SEC) can identify large insider trades placed just before earnings reports. The Dark Web is a safe haven for crime now, but it might not be in the future. Last November hedge fund billionaire Steve Cohen’s firm SAC Capital paid the largest insider trading fine ever, a cool $1.8 billion dollars.

Cities With The Best Public Transportation In The World (Ranked!)
The proliferation of decentralized exchanges and privacy-focused cryptocurrencies may further obscure the transit of money and make it harder to track financial activities. Dark web insider trading is not limited by geographical boundaries and coordinated international efforts are necessary to combat this threat effectively. These collaborative initiatives foster communication and enhance the collective response to cyber threats. Businesses face substantial cybersecurity risks due to the proliferation of these marketplaces. Data breaches often lead to sensitive corporate information appearing on the dark web, which can fuel further attacks.



