In the realm of cybersecurity, Dark Web monitoring tools serve as vigilant guardians, tirelessly scanning the digital horizon for emerging threats. These tools go beyond the superficial to shield you from precisely targeted attacks, such as counterfeit hacking attempts. Operating on the assumption that adversaries may lurk in the shadows of your system, these tools initiate thorough investigations to detect any anomalies or unusual behaviors that might hint at malicious activity. Dark web monitoring involves using specialised browsers with specific configurations to search for and analyse data on the dark web.

How Personal Information Gets On The Dark Web
From protecting your devices to shielding your online privacy and safeguarding your identity, our products provide a layered defense against hackers and scammers. You should also verify that proper offboarding procedures were followed when they left and consider conducting a broader review of your user account management processes. Many companies find that implementing automated offboarding workflows helps prevent these security gaps. Yes, finding your business information on the dark web is cause for immediate concern and action. Exposed credentials are frequently used for account takeovers, business email compromise, and more sophisticated attacks targeting your organization. Once your information appears on the dark web, it typically cannot be completely removed or deleted.

Integration Into Security Platforms
This might involve changing passwords, notifying affected parties, or working with law enforcement to address the breach. In wrapping up, dark web monitoring enables organizations to navigate the complex terrain of digital threats with more confidence. By delving into the depths of the deep web and areas beyond the reach of standard search engines, a robust dark web monitoring solution becomes indispensable.
Being one of the best dark web monitoring tools, ACID works throughout the year and investigates deeply into the dark web to find any clue of malicious activities targeting the clients. The most notable thing about this service is that it automatically and constantly updates the technological tools that deal with the latest threats and attack methods. All in all, dark web monitoring services are great tools for identifying the exposed data and the time your data remains exposed. Anyone committed to protecting their data, be it an individual or a business, must consider using them. A dark web monitoring service continuously scans the dark web to ensure an organization’s data remains protected from cybercriminals. It operates around the clock to promptly detect when sensitive information falls into the wrong hands.
Digital Shadows integrates seamlessly with existing security systems, enhancing overall threat detection and mitigation capabilities. By proactively monitoring talks and activity on the dark web, organizations can spot hazards to their reputation, fake goods, or unlawful use of their brand. We’ve covered how dark web credential monitoring works, but we haven’t gone into the details of where these shady deals take place. Not many know about the dark web, because most people will never reach these corners of the internet. You might be wondering how this can happen to you if you’ve taken all the necessary precautions.
SolarWinds Top 5 Essential IT Tools
One of the most interesting dark web data breach trends 2025 is the continued growth of cybercrime involving sensitive personal and financial data. As businesses increasingly store customer data in digital formats, cybercriminals are targeting this valuable information on the dark web. For instance, credit card details, banking login credentials, and personal identification numbers (PINs) are frequently traded on hidden marketplaces.
The Dark Web is often referred to as the seedy underbelly of the internet up to the brim with criminal activity. OpenCTI’s feature set includes role-based access control for your information security team, standards-based data models, and attribute data indicating the origin of the finding. ShadowDragon offers a robust suite of investigative tools tailored to streamline the complexities of modern investigations. Their product lineup comprises OIMonitor, MalNet, and SocialNet, each serving a distinct investigative purpose.
Mitigates Emerging Threats:
With pre-attack intelligence on the reconnaissance threat actors undertake on the deep and dark web. Spot the early warning signs of attack including insider threat, executive threat, and supply chain compromise before they impact your business. Newly identified vulnerabilities or exploits represent significant opportunities for threat actors, and these attack methods are discussed, developed, and sold in dark web forums and underground marketplaces. Because free Dark Web scanners are one-time services, they simply aren’t enough to keep you safe.
- Dashlane is a subscription-based password manager and digital wallet application that offers security tools for both businesses and individuals.
- Exploring the intricacies of dark websites reveals a complex underworld where cyber threats and criminal forums thrive.
- Our analysts rely on Lunar, a tool we’ve developed that lets users identify and act on potential threats in near real-time.
- Lunar by Webz.io is a comprehensive dark web monitoring platform that collects vast amounts of structured data across the open web, deep web, and dark web.
Integration With Existing Security Infrastructure

AI can scan images, QR codes, and screenshots shared on the dark web to identify threats. Yes, cybersecurity professionals analyze AI-generated reports to validate findings and prevent errors. AI cross-references exposed data with corporate or personal records to identify leaks. Our cutting-edge AI Call Notification feature ensures you’re instantly informed about any incidents.
Benefits Of Dark Web Monitoring By LifeLock
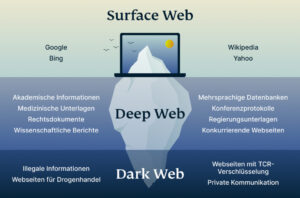
DarkOwl Vision is a cross between the CrowdStrike and Echosec services on this list. Like CrowdStrike, this system requires you to set up a list of identifiers for your company, which include domain names, addresses, and product names. In Deep Web/Dark Web terminology, the World Wide Web that the general public uses is called the Clear Web. This is a collection of websites that can all be accessed through a search engine. Organisations need robust technical infrastructure to support effective dark web monitoring. Hunchly is a web capture and investigation tool that also supports dark web investigations.
As organizations become increasingly digitized, cyber threats and data breaches also unfortunately increase. Threat actors can steal organizations’ data or human error and faulty security controls could leak data. Dark web monitoring is crucial as it helps businesses identify if they have any compromised sensitive data in illicit communities. This allows them to take steps to secure their networks and prevent further damage.
Firefox Monitor’s Top Features
At CMIT Solutions, we help clients identify early indicators of compromise by constantly scanning these hidden corners of the internet where hackers trade stolen information. Dark web monitoring is something that requires a lot of complex tools and expertise. Without using professional tools that have been specifically designed for the job, it is hard to find your information on the dark web, plus, it may mean having to access untrustworthy sites. Journalists and whistleblowers have been known to turn to this part of the internet to share information, but it is also used for criminal activities. Scammers can be found selling everything from counterfeit IDs to stolen credit card information.
Regularly educate staff about the latest phishing tactics, social engineering schemes, and safe online practices. Establish clear policies regarding the handling and sharing of sensitive information. Dark web monitoring can uncover sensitive information about clients, employees, and executives that appears on the dark web. With this information, companies can take action to prevent criminals from exploiting the stolen data. On the other hand, the dark web is subsequent, which can be accessed by special tools like Tor, I2P, and Riffle. The deep web is utilized for legitimate day-to-day online activities, but the dark web is more anonymous and famous for illegal activities or transactions.
This can include monitoring for particular keywords or phrases related to a company or individual, such as login credentials, financial information, or personal data. The goal of dark web monitoring is to identify potential threats and vulnerabilities before they can be exploited by cybercriminals. By identifying these threats early, you can take proactive measures to mitigate the potential damage involved, and launch the incident response procedures. OWASP TorBot is a free dark web scanning tool written in Python, designed for crawling hidden websites with .onion addresses.
You may hear the term “dark web scan” and wonder how it’s possible for a solution to scan the entire dark web – especially if it’s so hard to access and it’s anonymous. When you hear the term dark web scan, what’s really happening is your credentials (like email addresses) are being checked against a database of credentials from known breaches. At LastPass, this service is provided by our partner Enzoic and in keeping with our zero knowledge model. We’ll also notify you of potential threats, like weak passwords, so you can stay ahead of hackers. The security tool asks users to enter their email addresses, continuously scan breached credentials within a database, and immediately alert them if they have been compromised.