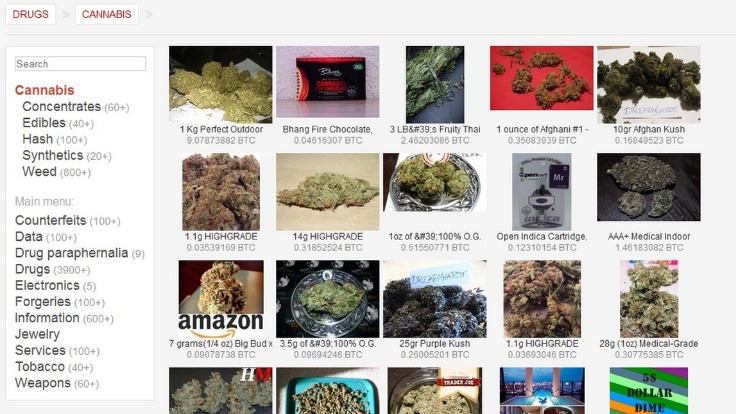
Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces
In some cases, established sellers on closed-down markets are welcomed onto new markets as digital “refugees” and have joining fees waived. More often than not, law enforcement is targeting the sellers more than the buyers. Still, it isn’t unheard of for people to be arrested for buying drugs on DNMs. It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack.
Proliferation Of AV Evasion Tools (Cryptors)

Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test.
Did The Silk Road Marketplace Go Under?

Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions. Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA.
What Is A Dark Web Alert? A Guide For Businesses
Concerns about how Meta treats user data have led many people to delete their Facebook profiles or at least limit their social media presence. Onion sites, or dark web websites, are sites on the dark web that can typically only be accessed using special software like the Tor browser. These sites use “.onion” domains, which are made up of random letters and numbers up to 56 characters long. Dark web websites won’t show up on Google, but they are indexed by dark web search engines such as Torch.

Indicators Of Compromise In Threat Intelligence
However, engaging in illegal activities on the darknet is against the law and can result in serious criminal charges. If you access illegal content or participate in criminal transactions, you face legal consequences. The legality depends on your activities and your country’s specific laws regarding darknet use. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents.
Stick to trusted sources and use caution when navigating the dark web. SecureDrop is an anonymous file-sharing platform designed for secure communication between whistleblowers and journalists. While anyone can use it, it’s built for high-stakes exchanges, making it overkill for routine file sharing or data backups. Major news outlets like The New York Times, The Economist, and The Guardian host SecureDrop instances on the dark web to give sources a safe, anonymous way to share sensitive information.
- Known for its robust escrow security and diverse offerings, Abacus is a top choice for 2025.
- Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace.
- These features help create a sense of ‘trust’ among users, even in the criminal ecosystem.
- Preventive Approach participates in various affiliate marketing programs, which means we may get paid commissions on editorially chosen products purchased through our links to retailer sites.
Before these dark web marketplaces were shutdown, they sold a range of illegal products, from drugs to firearms. Your definitive guide to the top darknet marketplaces of 2025—featuring verified onion routing links, cryptocurrency trading insights, vendor ratings, and escrow security details. Dive into the dark pool trading world with Abacus, Alphabay, Torrez, and more. Moreover, 66% of migrating users choose to move their activity to the same coexisting marketplace. In a world where data is a valuable asset and cyber threats evolve rapidly, understanding how dark web marketplaces operate is essential. While the anonymity they offer can embolden criminals, staying informed and taking preventive actions are key to remaining secure.
Microsoft Strengthens Security After China-Linked Attacks
It has been in operation for more than a decade since its debut in 2014. Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity. You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. The Silk Road dark web marketplace changed the way cybercrime operates, showing how technology like Tor and Bitcoin can facilitate anonymous transactions.
- Once the buyer confirms satisfaction, the funds are released to the seller.
- Market listings on these platforms often carry the same professional touch you’d expect from legitimate sites complete with product descriptions, seller ratings, and even customer reviews.
- They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation.
- Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing.
- In some cases, established sellers on closed-down markets are welcomed onto new markets as digital “refugees” and have joining fees waived.
Stolen Data Ecosystem
Working with our international partners in the United Kingdom, Germany, and Turkey, the FBI conducted a two-year undercover operation to penetrate the organization and bring it to its knees. Using undercover techniques, the FBI penetrated the highest levels of this group and identified and located its leading members. Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data. However, these platforms often faced law enforcement takedowns, technical issues, or exit scams, where operators vanished with user funds. Keeping an eye on the dark web is no easy task, but law enforcement and cybersecurity pros have some pretty advanced tools up their sleeves.

Fraudsters create fake versions of popular darknet sites to trick users into entering login details or personal data. If you fall for it and log in, they immediately steal your credentials and either sell or use them for other scams. Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you? Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device.
Why Third-Party Risk In Healthcare Demands Immediate Attention

This market specialized in selling marijuana related products and magic mushrooms, with no “hard drugs” for sale. The Silk Road was the first popular DNM which appeared on the scene in back in 2011. Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more.
Top 20 Benefits Of Using Agentic AI For Businesses
This incident underscores why dark web monitoring is essential to prevent data breaches for small businesses. A dark web monitoring tool could have detected the compromised credentials early, enabling the firm to reset passwords before the attackers acted. Furthermore, regular cybersecurity risk assessments would have identified weak authentication systems, allowing the firm to implement stronger measures, such as multi-factor authentication.
Cybercriminals are expected to exploit trusted company-contractor relationships, breaching contractor systems to access corporate data. This tactic, seen in 2024 with incidents involving Ticketmaster and IntelBroker, could lead to an overall rise in data breaches. The number of malicious tools, or “drainers,” designed to steal cryptocurrency assets like tokens and NFTs saw a substantial rise. Unique threads discussing drainers on dark web forums increased from 55 in 2022 to 129 in 2024, with Telegram channels serving as prominent hubs for these activities. 85% of top markets now use escrow security, up from 60% in 2023—see Alphabay. We have simplified the cybersecurity assessment process and made it accessible for all businesses.
Dark web websites look pretty much like any other site, but there are important differences. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.



