
Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics.

In this era, it takes one wrong click and all your sensitive data ends up in the wrong hands. Therefore, you need to take your privacy seriously and start by using strong and unique passwords for every online account you open. Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer. The closure led to the arrest of the platform’s founder Ross Ulbricht. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine.
From Silk Road To RapTor: The Evolution Of Darknet Markets
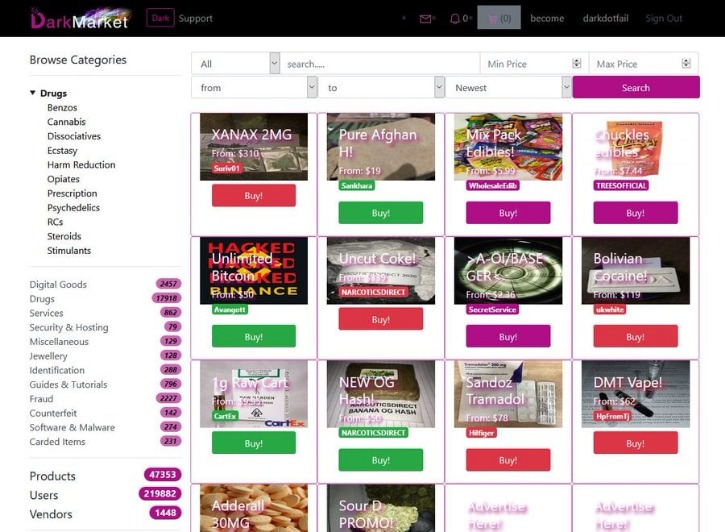
The goods on sale range from stolen credit card data and forged documents to illegal drugs, weapons, malware as a service, and hacking tools. Darknet markets are platforms that are only accessible via the Tor network, enabling anonymous transactions between buyers and sellers. These marketplaces are designed to provide a secure and private environment for exchanging goods and services. Accessing these markets requires the Tor network, which ensures anonymity by encrypting traffic through multiple layers. Cryptocurrency payments are the norm, with Bitcoin (BTC) and Monero (XMR) being the most popular options, Monero often favored for its privacy features. Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices.
This was the initial framework for anonymous communication and file sharing. Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software. It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up.
Public Token Treasuries And Tokenization Are Fantastic For Crypto, But Risks Remain, Binance’s CZ Says
To access sites in the Darknet, users need to use special software such as the Tor Browser as they are on an encrypted network to hide the identities of the people running the sites and services connected to them. The most recent example is the shutdown of the oldest marketplace Hydra Market in 2022 which took a combined effort of the FBI and the German authorities. Unfortunately, that as well didn’t stop other darknet markets from rising. Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web.
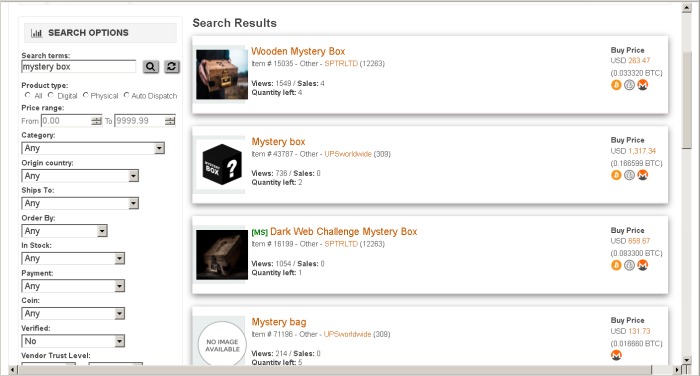
Some dark web listings claim to offer services like hacking-for-hire or even hitmen. DarkFail has been a darknet user’s companion since 2017, providing thoroughly vetted information on the best darknet markets, products, vendors, and security practices. Dark web markets are hidden online platforms in Tor where users anonymously buy and sell goods and services. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof.
It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy.

Exploitation Of Anonymity For Harm
Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name.
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity. Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity and expose users’ real-world identities. Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). These technologies obscure users’ identities and locations by routing their internet traffic through multiple volunteer-operated servers worldwide, making it extremely difficult to trace activities back to individuals.
Best Darknet Markets For Safe Drug Deals In 2025
- The darknet can take care of this (and much more) by discretely delivering the legal compound to your door with no questions asked.
- The investigation uncovered a local criminal organization linked to a large international drug supply operation.
- The S2S network is mostly populated by U2U-only sellers, followed by market-only, and market-U2U (see Supplementary Information Section S5).
- Always verify URLs, use encryption, and be aware of scams to ensure a secure experience.
- Over the next two years, the Silk Road set the standard for darknet marketplaces.
- Activities on dark-web marketplaces are closely monitored by international law enforcement agencies.
The cost can be exorbitant, but for victims, it’s always higher and devastating. For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion.
Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
The Marketplace As An Arsenal
From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. AlphaBay and other markets of this period implemented multisignature transactions, stronger encryption protocols, and improved escrow systems. Operation Bayonet in 2017 demonstrated the vulnerability of centralized market structures to coordinated international law enforcement. While mainstream discourse often focuses on illicit activities, these markets also represent significant technological innovations in privacy, digital payments, and trust systems in decentralized environments.
Featured Products Tor2Door
- The best darknet markets in 2025, such as Nexus and Abacus, offer reliable escrow systems and encrypted transactions.
- It asks you to pay the merchant fee if you want to sell something, preventing the buyers from getting scammed.
- Market lists curated by trusted communities help users avoid scams, while Tor-based interfaces ensure anonymity.
- The website has a great design and a clean and organized interface that is easy to use.
- The reduced accessibility of Monero forced users to rely on a more liquid and widely accepted asset,” Jardine stated in an interview with CoinDesk.
Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. Archetyp is one of the most sought-after and popular darknet marketplaces in European countries, with a unique combination of features and functions. Its interface is characterised by simplicity and convenience, which has earned it high marks from users in numerous surveys… By following these security best practices, using escrow, and being cautious with your data, you can navigate them safely.
The dark web is an anonymized overlay of the internet accessible through networks such as Tor (“The Onion Router”), I2P and Riffle that utilize layered encryption to obscure the identities and locations of users. Many suppliers around the world work with Tor2Door darknet due to the fact that the Tor2Door darknet shop has the lowest commissions on the market, as well as a well-deserved reputation among sellers. The smooth operation of Tor2Door darknet market is due to the fact that Tor2Door market has powerful protection against various DDoS attacks, as well as other methods that will interfere with the operation of the site.
Despite consistent results, this study has limitations that may be addressed in future work. First, while the dataset is preprocessed with state-of-the-art methods, there is no ground truth for validation, and this uncertainty propagates to our findings. For instance, we cannot verify if an entity classified as seller is in fact a seller. Similarly, there is no unique choice for the classification parameters or ground truth for fitting them. In light of this, we have chosen the parameters conservatively, obtaining estimates for the number of sellers that are in general smaller than the ones produced by other methods.



