If you just want to go ahead and learn how to access the Darknet, you can skip to the bottom of the post and watch the video tutorial. “Bitcoin is expensive and highly volatile, so $100 today might be $60 tomorrow (or $160),” Terence told me. Since some of these groups or operations don’t necessarily rely on traditional foundations – such as banks, suppliers, etc. – they can still continue to exist.

Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025
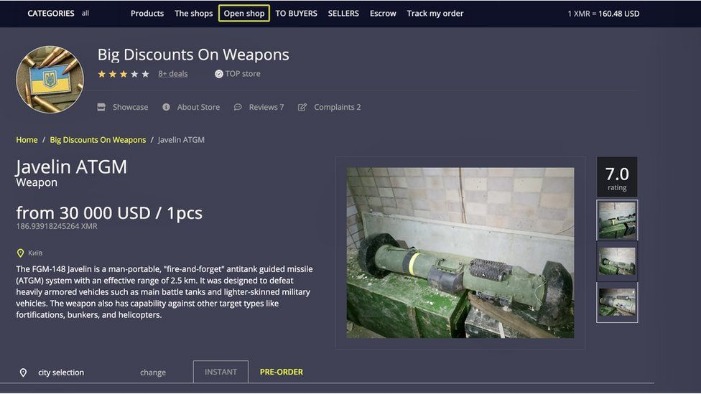
It’s designed as an environment to elude detection, where site owners and visitors hide their identities. And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. Established in 2019, Versus quickly gained a reputation for a user-friendly UI and intuitive search options. These markets are often used for the sale of illegal goods and services, such as drugs, weapons, and stolen data.

The Full List Of Trusted Darknet Markets:
When transferring cryptocurrency, make sure to use a secure wallet and double-check the recipient address before sending any funds. It’s also a good idea to use a cryptocurrency tumbler or mixer to further obscure the origin of your funds. By comparing our measures of the types of counterfeits to goods seized at borders, we can identify how products differ and discuss possible contributing factors to those differences. Also, the distribution of counterfeits found on dark markets and seized products varies greatly. The remaining categories show a similar distribution (OECD/EUIPO, 2019). For example, many companies affected by counterfeiting operate across nations, affecting the ease with which authorities can monitor and combat counterfeits.
Tor is a network of volunteer relays through which the user’s internet connection is routed. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information.
Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN. This means the VPN provider doesn’t see your real IP address and the VPN protects you from those bad exit nodes. Dark net websites are called “Tor hidden services”, and they can be distinguished from normal websites by their URLs. The original owners are locked out of these accounts, unable to unlink their card details from them. The only solution in these situations is to cancel the attached credit or debit card.
Method II – VPN Over Tor
- Darknet Markets, also known as cryptomarkets, are websites hosted on the deep web which can only be acessed through anonymous web browsers like the TOR.
- While some darknet markets are scams or honeypots set up by law enforcement, many are legitimate and provide a valuable service to their users.
- Unlike many other dark web markets, Cypher does not require buyers to deposit cryptocurrency upfront, which reduces the risk of exit scams.
- Nevertheless, most people on the internet do not need to communicate or venture into the dark web.
To avoid immediate shutdown, the servers hosting DNMs must be in countries with lax legal regulations. This means the server admins must pay significantly higher hosting fees than they would on the clearnet, for less reliable service. DNMs may start when a single person, or a small group of people, decide to build one.
Explore Dark Web Marketplace Links With Confidence
Of all listings (excluding those selling drugs), 60% could potentially harm enterprises. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. The market is especially well-known for providing access to freshly compromised data, often obtained from recent breaches and stealer logs. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. Since its inception, the market has catered to criminals looking for high-quality counterfeit items, such as fake IDs, passports, and branded luxury goods.
What Do People Sell Or Exchange On Darknet Markets?
It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. Founded in 2014, BriansClub remains one of the oldest and most infamous dark web markets for stolen credit cards, fullz (complete identity kits), and dumps. To buy from the darknet markets, you’ll need to fund your account with Bitcoin or another cryptocurrency.
Dangerous Fake Or Malicious Vendors
A quick and relatively private way of doing so is to use a peer-to-peer market such as Localcryptos.com. This enables you to buy bitcoin from private individuals, who will accept payment into their bank account, as well as alternative methods such as Paypal, Alipay, and Moneygram. A full explanation of how to make a bitcoin purchase on Localcryptos follows below.
How To Stay Safe From Dark Web Threats

This is because darknet markets are only accessible through the Tor network, which provides anonymity and encryption. To access these markets, you will need to download and install the Tor browser. Below, we have another version of this chart showing only markets with a global customer base. Keep in mind that we don’t recommend our readers visit dark web marketplaces themselves.
- If the site hasn’t loaded after 30 seconds, refresh it or try an alternative site.
- You will then be prompted to enter your email address, followed by the four-digit verification code you’re emailed, followed by your personal details such as address and credit card number.
- We’re back with another video in our Webz Insider video series on everything web data.
- There are a lot of illegal things being done on the dark web, and participating in such activity can come with serious legal consequences.
When purchasing LSD from darknet markets, it’s essential to find a reputable vendor. Look for vendors with good reviews and high ratings to ensure the quality of the product. Many items sold on darknet markets are illegal, and purchasing them can lead to legal consequences. And then there’s the bad stuff – contract killers, child porn, drugs, and other nasty stuff which share the same benefits of anonymity as the good sites. It’s one of the reasons why they often resemble sites from the early 2000s. They’re generally quite lightweight, so you don’t even need a fast connection to access one.
Cybercrime Increasingly Moving Beyond Financial Gains
Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces.
Tips To Stay Safe When Using The Dark Web
Such content fuels a dangerous cycle of abuse, violence, and exploitation. Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random. These nodes encrypt your browser traffic in layers at each node hop on its way to/from the source (your browser) and the destination (a hosted hidden service). In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game.



