For example, purchase drugs or firearms through the dark web is illegal, and you’ll be held liable for your actions. The deep web is referred to as anything online that can’t be accessed by using a search engine. This means the mail in your Outlook inbox, direct messages (DMs) on social media, and even your private Facebook photos. Operating since 2015, Nulled is an English-language forum infamous for hosting leaked databases, cracked software, and identity dumps. Despite suffering a breach itself in 2016, it continues to be a go-to destination among dark web forums due to its vast range of illicit content and tools. Among the most infamous dark web forums, BreachForums rose to prominence after the takedown of RaidForums.
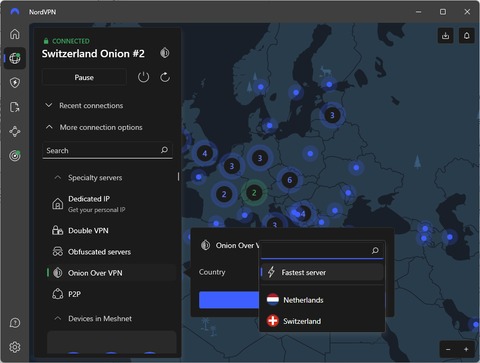
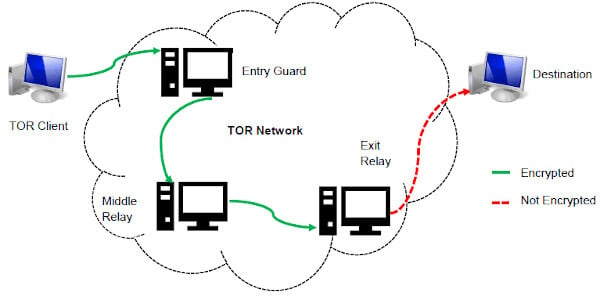
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. For this reason, you must watch out and avoid opening anything that looks suspicious to you. Your online activity and communications remain private and secret on the dark web.

Debian Project On Tor
- Stay vigilant, trust your instincts, verify sources, and prioritize your security to make the most of the anonymity these networks provide.
- Since the dark web is hidden from the surface web, these dark web search engines allow users to explore the concealed part of the Internet.
- I also like that the security guides are user-friendly — the format is easy to scan, complicated terms are explained very well, and there are videos and screenshots.
- You can access onion sites only through the Tor browser or special network configurations.
- ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy.
However, it’s not as detailed as The Hidden Wiki, and you may need some time to get used to its interface and how to find your required link. Candle is a lightweight, open-source dark web search engine with basic search functionality and high speed. Ahmia is considered one of the safest because it filters out illegal content and has strong moderation. Yes, DuckDuckGo has a .onion version that works through the Tor browser for anonymous searching. You can’t access the dark web without the use of an anonymous browser known as Tor.
For example, there are separate categories for blogs, email services, file uploaders, forums, and more. I tested all the website links on The Hidden Wiki and almost all of them work (I was able to access sites like Deep Web Radio and ProPublica without any issues). Dread is the most active, functioning like a Reddit-style message board where users discuss everything from Tor security to reviews of dark web services. Hidden Answers, on the other hand, is more like a dark web version of Quora. It allows anonymous users to ask and answer questions on controversial or privacy-sensitive topics.
- Bitcoin fog is just one of the many crypto tumblers available to dark net users; there are however several other popular Bitcoin Mixers on the dark net as well.
- Since these markets operate in hidden networks, scams and security risks are common.
- On the dark web, links could be a step in the right direction to address this issue.
- SecureDrop helps whistleblowers anonymously send sensitive material to media outlets via a unique SecureDrop URL.
SecureDrop
First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses. Check for recent user reviews or feedback to ensure the site is still operational and legitimate. Always use PGP keys when available to verify the identity of marketplaces or services. Another good practice is to cross-reference links with multiple sources to confirm consistency.
What’s The Difference Between Surface Web And Dark Web Search Engines?
Accessing it is not as complicated as it sounds, but doing it safely matters. It can be risky if you’re not careful, so follow these simple steps to explore it without exposing your identity or data. In short, if a page requires a login, subscription, or isn’t linked publicly, it’s part of the deep web.
What Kind Of Content Is On The Dark Web?
Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download.
MICROSOFT SECURITY TOOLS

Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. Wasabi is one of the most popular cryptocurrency wallets on the dark web. It allows you to search for images, maps, files, videos, social media posts, and more. It may initially look abandoned, but the community members will answer your questions. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
Accessing tunnels is illegal and dangerous, which is why records of these “adventures” can only be found on the dark web. If you want to access this site, do it only for fair purposes and with proper security measures. Sci-hub is a helpful dark web platform for those looking to access important research blocked by a paywall. You can access almost any published paper that would have otherwise been hidden behind a paywall. Therefore, you will always find updated search results while using this service. To send a message or image via ZeroBin, you just need to copy the desired content and paste it into ZeroBin’s editor.
Helping Users Navigate The Dark Web Safely

Even a single wrong character in a .onion A URL can lead to scams, malware, or fake marketplaces. That’s why relying on trusted onion directories like Ahmia, Dark.Fail, OnionLinks — and the real Hidden Wiki — are essential. ZeroBin allows users to post encrypted text that even the host server can’t read — perfect for pasting links or messages securely.
For those needing an additional layer of security, you can set it to disappear right after viewing. Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages. It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for.
DuckDuckGo (Dark Web Version)
While they have gained notoriety for the sale of banned substances and illegal goods, many markets focus solely on legal products. These platforms offer a wide range of products and services, both legal and illicit. It’s a search engine that allows users to find products listed for sale on various Darknet Markets. From the number of daily users to the distribution of relays worldwide, this platform provides a comprehensive overview of the Tor network’s health and performance. However, its .onion service underscores the agency’s recognition of the importance of secure, anonymous browsing. When accessed via the Tor network, Tails provides an array of tools optimized for security, from web browsers to email clients.
Laws pertaining to anonymity and the use of privacy-enhancing tools vary widely from one country to another. While accessing the dark web may be perfectly legal in some regions, other places may restrict or scrutinize such activities more heavily. Engaging with certain types of content—such as copyrighted materials, illegal drugs, or illicit services—can lead to serious legal consequences. If you’re unsure about the legal boundaries in your country, consulting a knowledgeable attorney or reviewing reputable sources of legal information is a prudent first step. N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks.
Together, these technologies facilitate private, censorship-resistant access to hidden content, with the Hidden Wiki acting as a trusted directory to navigate this complex landscape. Without these tools, neither Google nor any surface web browser can reach these secure, hidden parts of the internet. This includes password-protected sites, private databases, academic journals, and, notably, dark web services accessible only through networks like Tor or I2P.