
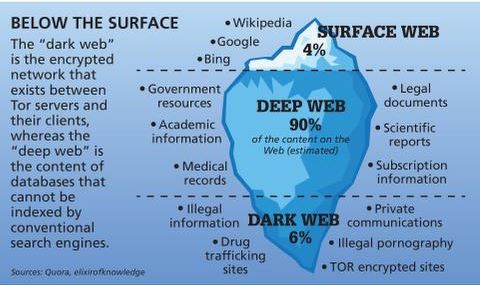
And when tech companies cooperate fully, encryption and anonymization can create digital hiding places for perpetrators. Facebook announced in March plans to encrypt Messenger, which last year was responsible for nearly 12 million of the 18.4 million worldwide reports of child sexual abuse material, according to people familiar with the reports. Reports to the authorities typically contain more than one image, and last year encompassed the record 45 million photos and videos, according to the National Center for Missing and Exploited Children. The darknet provides a haven for those who want to go unnoticed, including those who are keen to break laws.
Child Abuse On The Dark Web
But on Wednesday, officials revealed that 337 suspected users had been arrested across 38 countries. It was shut down last year after a UK investigation into a child sex offender uncovered its existence. The site had more than 200,000 videos which had collectively been downloaded more than a million times. In today’s digital era, where information is constantly on the move across all digital platforms, an… The US government created the dark web to help its spies communicate and exchange information securely. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder.
The COVID-19 resource centre is hosted on Elsevier Connect, the company’s public news and information website. These permissions are granted for free by Elsevier for as long as the COVID-19 resource centre remains active. To protect yourself while browsing the dark web, it’s essential to use security measures such as updated antivirus software, a secure VPN, and the Tor browser configured with appropriate privacy settings.
Protecting Your Teen From The Dark Web
Offenders were also documented sharing advice and even AI models fed by real images with each other. Start your digital parenting with deliberate restriction of content (e.g., no social media apps in elementary school). As your child gains experience and judgment, slowly loosen up and allow more digital freedoms, with tech monitoring and frequent check-in discussions. Avoid dishonest spying that can lead to a hurtful ambush that will blow your credibility. If you’re straight with them that you will check their online content, they’ll post with better judgment and accountability from the beginning.

A recent effort led by German police, and involving others including Australian Federal Police, Europol and the FBI, resulted in the shutdown of the illegal website Boystown in May. Online privacy advocates including Edward Snowden have championed the benefits of such platforms, claiming they protect free speech, freedom of thought and civil rights. The focus shifted to tracking these users after the website was seized last year. Prosecutors say they conducted 92 searches of homes and businesses tied to U.S. suspects, with 53 arrests so far.

Encrypted Communication Tools
These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P.

Site Search Navigation
For teens in the dark web, these hidden spaces may represent the ultimate escape from the rules of their everyday internet. By exploring these 7 startling insights, we can uncover what this trend says about the evolution of youth identity in the digital age. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website.
Shareable Text-based Detection For CSAM
There seems to be no precedent, however, as officials could not cite a single prior case resulting in federal charges, the Post reported. This “explosion” of “disturbingly” realistic images could help normalize child sexual exploitation, lure more children into harm’s way, and make it harder for law enforcement to find actual children being harmed, experts told the Post. Global child protection groups are increasingly concerned about predators using the site to gather self-generated child sexual abuse material. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.

BBC Tor Mirror
- It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity.
- And in some cases cops defeated user attempts to hide their identities—such as a man who made payments using his mother’s name in Spain, a local news outlet, Todo Alicante, reported.
- Children, raped by relatives and strangers alike, being told it was normal.
- Many actors enhance their operational security by using virtual phone numbers and turning to Telegram’s Secret Chats for fully encrypted communication.
There is a cohort of darknet forum members that discuss wanting to seek help to stop engaging with CSAM (Insoll et al. 2022). However, due to the suspicious disposition of CSAM forum members, there may be a reluctance by them to engage with therapeutic interventions advertised on the clear web. Further research is needed to develop deterrence and intervention strategies within these CSAM darknet forums, which could potentially reduce the number of potential or onset individuals accessing CSAM. The rise of social media also gave rise to dedicated online forums focusing on “child love” (Goldman and Ronken 2000). Before, support groups had been a local matter, their clientele mostly coming from the city they were held in. Social media changed this and allowed associations with like-minded others from across the globe.
Report It To The Authorities (if It’s Safe To Do So)
Think of it as walking down a dark, unlit alley in an inner-city neighborhood. Clicking on an innocent-sounding link may actually take you to a site displaying graphic abuse. There is a high chance, even if your child is just browsing, that he or she may stumble upon something that is truly horrific. While this can happen on the regular internet as well, it happens more frequently, and spontaneously, on Tor.
“You are unable to live in civilized society without harming children,” she said, before ordering what amounts to a life sentence. McIntosh revealed some of those offenses voluntarily in interviews with investigators, Serafini said. Though his codefendants didn’t disclose prior instances of abuse, the attorney called it “wildly unlikely” that their involvement in the website was their “first rodeo.” Though Schiller suggested that McIntosh’s history of abuse made him the worst of the site’s four leaders, Serafini disagreed. Serafini called the site “horrific” and blamed McIntosh’s involvement on a lifelong sexual addiction.
- Some countries and ISPs may try to prevent access to DuckDuckGo’s direct link.
- This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to.
- This close relationship with tech companies may ultimately be in jeopardy.
- They are trying to create their “brand.” And what models do they have for branding?
- Accessing software such as TOR is not illegal and not all content on the dark web is illegal.
“Some of those arrested not only uploaded and watched videos but also abused children,” Europol said, while confirming that “the investigation is ongoing,” making it appear likely that more arrests could follow. Arrests spanned the globe, including 16 in Spain, where one computer scientist was found with an “abundant” amount of CSAM and payment receipts, Todo Alicante reported. Police also arrested a “serial” child abuser in the US, CBS News reported. When such operations are taken by LEA, community members of a “taken down” site will “go quiet” become inactive for a number of days.
Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. Rather than viewing this exploration as purely negative, understanding the “why” behind these behaviors offers perspective. Adolescents aren’t drawn solely by thrill-seeking; many are testing boundaries, forming identities, or challenging norms. Recognizing these patterns can foster conversations that guide them toward healthier engagement. Creating an environment where online behavior can be openly discussed is essential.



