
Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.
I Found The Easiest Way To Delete Myself From The Internet – And It’s Fast
Whether you’re looking for stronger privacy, a simple interface, or a tool designed specifically for hidden services, there’s likely an option that fits your needs. Think about what matters most for your browsing and security, and make informed choices to navigate the dark web safely. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
- In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis.
- Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution.
- Unlike the publicly accessible surface web, the deep web includes sites requiring login credentials but is still accessible via traditional browsers.
- The dark web, an even more puzzling sublayer, exists within this hidden world.
- Then, click on New Tor circuit for this site, as illustrated below.
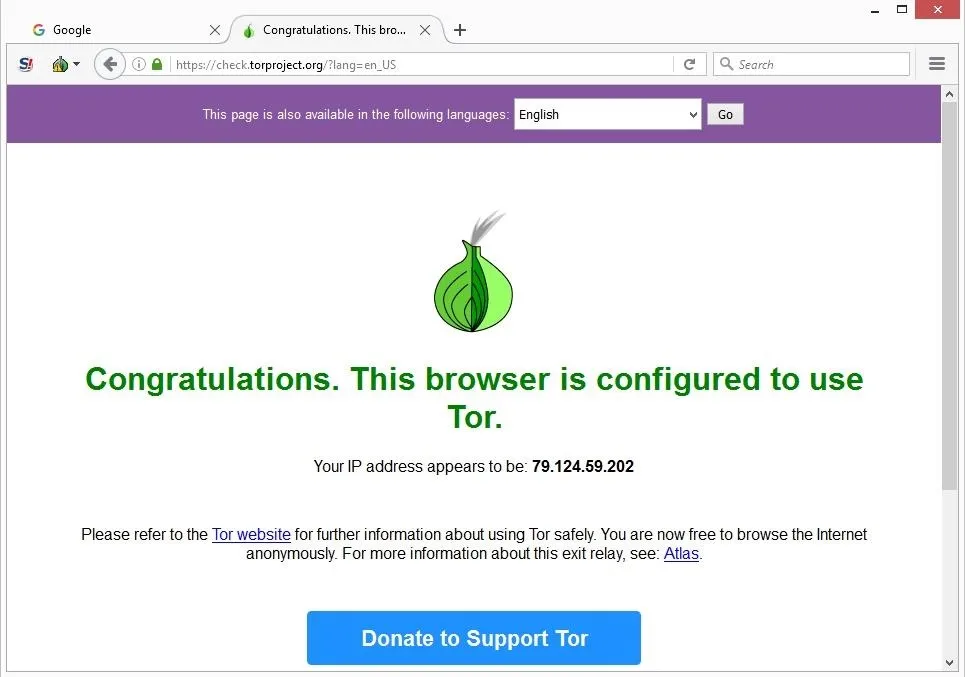
- The Deep Web includes unindexed content like private databases and password-protected sites accessible with standard browsers.
Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. The first step is to download and configure the Tor browser from its official website.
How To Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL
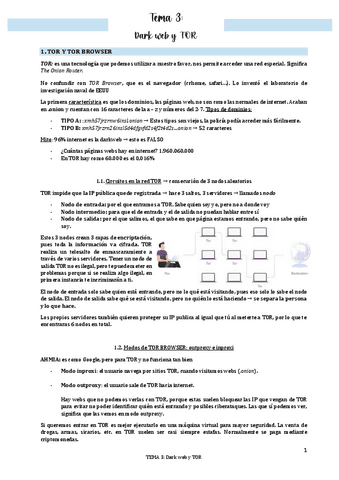
Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S.
Does Tor Slow Down My Internet Connection?

Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start. HTTPS uses a Secure Sockets Layer (SSL), which encrypts and authenticates information going between a browser and a website, and between servers. Never put your personal info into an HTTP site, whether it’s in Tor or on the surface web. See a rundown of a VPN vs. proxy vs. Tor for all the pros and cons. Or if you’re new to the VPN world, see what a VPN is and why you should use one.
It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. Check out these best onion sites to access the dark web securely and anonymously. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays.
Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country. These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet. But while Tor encrypts your traffic, it doesn’t hide the fact you’re using it. If you’re new to Tor, setting up the browser software and connecting to the network might seem intimidating, but it’s actually straightforward.
Remember, while these tips can significantly enhance your safety and security, there is no foolproof method to eliminate all risks. Practice discretion, stay informed about current security practices, and always prioritize your online safety when using the dark web. By following these steps, you are on your way to exploring the hidden depths of the internet and enjoying a heightened level of online privacy and anonymity.
What Is The Difference Between Tor And A VPN?
Beneath this lies the “deep web,” a significantly larger segment encompassing content not indexed by these search engines. This includes resources requiring specific credentials or access, such as online banking portals, private databases, and academic journals. The “dark web,” in contrast, represents a deliberately concealed subset of the deep web. Access to this layer requires specialized software and techniques, with Tor Browser being the primary tool for this purpose.
How To Stay Safe While Using Tor
You can usually select the location you want to appear to originate from and VPNs will use a collection of servers and relays to make tracing your IP difficult. However, today’s most popular search engines — including Google, Bing, and DuckDuckGo — only index a portion of the internet. Husain Parvez is a Cybersecurity Researcher and News Writer at vpnMentor, focusing on VPN reviews, detailed how-to guides, and hands-on tutorials.
Featured Articles
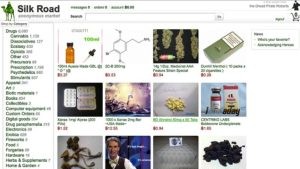
It aims to expose abuses of power and betrayal of public trust through investigative journalism. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it.
Other Ways To Access Dark Web Platforms
You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions. If you plan to purchase on a dark net marketplace or dark web commerce sites, you’ll need to create a fake identity. Remember only to make purchases using digital currencies and never provide any online banking login details. DuckDuckGo is a privacy-focused search engine that works as Tor browser’s primary search engine. It doesn’t track searches or store personal data, making it a strong option for users seeking more anonymous private browsing. However, DuckDuckGo doesn’t index dark web content — it only accesses surface and deep web sites through Tor.
- Learn how to set it up, explore what it does best (and where it falls short), and discover why pairing it with a trusted VPN could give you stronger, layered protection against prying eyes.
- In a world where online privacy is constantly under threat, the Tor Browser offers a powerful tool for safeguarding your identity and protecting your digital footprint.
- And HTML5 audio and video, as well as WebGL, become click to play.
- The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access.
- Some of the reasons why it’s worth monitoring these hack forums include, ability to detect breaches early, gaining threat actor insights, and third-party risk mitigation.
Subscribe To A Formidable VPN
This level only allows website features required for static sites and basic services. Javascript is disabled by default on all sites; some fonts, icons, math symbols, and images are disabled; audio and video (HTML5 media) are click-to-play. Tor aims to provide protection for ordinary people who want to follow the law.
Our goal is to deliver the most accurate information and the most knowledgeable advice possible in order to help you make smarter buying decisions on tech gear and a wide array of products and services. Our editors thoroughly review and fact-check every article to ensure that our content meets the highest standards. If we have made an error or published misleading information, we will correct or clarify the article. If you see inaccuracies in our content, please report the mistake via this form. The dark web is a double-edged sword, offering anonymity but also posing significant risks.
Due to all the nodes that your traffic passes through, Tor by itself significantly limits bandwidth. Adding a VPN to it, even a fast one like IPVanish will make it even slower, so please be patient. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method. In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely.


