Our team is a group of privacy advocates who want to create an open and fair internet. While the Deep Web largely provides a safe sanctuary for valid and secure information, the Dark Web presents many ethical, legal, and safety challenges. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
Risks Of The Dark Web
While some users leverage this anonymity for noble causes, others push the boundaries of legality. These realms emphasize online privacy but cater to very different crowds. Whether it’s the vast but secretive Deep Web or the dark, intriguing nooks of the Dark Web, both have their places in the digital age, serving needs from the ultra-private to the overtly hidden. It comprises darknet markets and hidden services within specialized frameworks like the Tor browser bundle. Here, it’s a wild west of content, from illegal drugs to black market weaponry.

Dark And Deep Web Monitoring For Effective Threat Exposure Management
Securing this data prevents it from being compromised and possibly showing up for sale on the dark web. However, the deep web can also host illegal content such as pirated media. Anyone can access this material without needing a different web browser such as Tor. Many websites on the deep web avoid showing up in search engine results by blocking the bots that ‘crawl’ the internet to collect information for search engine indexes. Other options exist, but they are generally created to fulfill specific purposes, such as file sharing. On the other hand, one cannot visit the dark web without purpose-built software.
CISO’s Guide To Threat Intelligence 2024: Best Practices
One cannot reach the Dark Web so easily since they have created strong encryption that is unreachable to the average user. Internet is a virtual world with billions of devices which means there is uncountable internet traffic. The Deep Web and Dark Web are part of the overwhelming virtual world. To use these browsers and their functionalities and understand the difference between Deep Web vs Dark Web, you need to read this blog till the end.
Key Differences
The Dark Web refers specifically to websites and services hosted inside Darknets. Search engines do not index these sites and use domains like .onion (for Tor) or .i2p (for I2P). Understanding the Deep Web and Dark Web can help you navigate the internet with greater awareness. While the Deep Web supports daily privacy, the Dark Web offers enhanced anonymity with some added risks. Knowing how these areas work helps us make informed decisions about online safety and privacy.
Legal Implications
Understanding the relationship between Tor and the dark web is essential—Tor (The Onion Router) is the primary software used to access these hidden sites. Discover the key differences between the Dark Web and Deep Web, their uses and risks to businesses. See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future. The dark web is far from an illicit-themed zone but rather a liberating site for journalists and activists, for instance, to converse privately in constrained freedom-of-speech environments.
Top Cybersecurity Discord Servers To Join
However, threats can often originate in the deep web before escalating to the dark web. The dark web is the traditional place for threat actors to engage in cybercrime through selling stolen credentials, sharing guides for techniques, posting ransomware victims’ information, and more. While Tor protects you and gives you anonymity on the dark web, we recommend that you don’t use the dark web. If you still wish to access it, don’t use your regular email and ensure your Tor applications are updated. Avoid downloading files as they are often filled with viruses and malware. Acessing does the dark web does not automatically place you in danger, but it is very easy to be caught unaware if you are not familiar with how it works.
Since the Dark Web is a collection of websites that are only accessible via darknets, let’s take a moment to define what darknets are. Darknets are encrypted overlay networks that sit on top of the public Internet. These include peer-to-peer and privacy-focused networks and can only be accessed using special tools like the TOR browser.
- Only concerned people have access to it and it is encrypted and password protected.
- People use it to share information when their local governments act hostile or snoop extensively.
- Misconfigurations, weak authentication, or stale credentials can expose private content—leading to unauthorized access, data leakage, and compliance issues.
- The internet was created in 1983 and has become a key part of our everyday lives.
- Normally, search engines will not turn up these types of search results if you try to access them.
- You may have heard of the terms shadow web, dark web and deep web is used when referencing the internet but aren’t quite sure what they mean.
Managing Cyber Risk With Check Point
Deep web concerns revolve around internal controls, access processes, and compliance readiness. Dark web concerns focus on external intelligence, early warning signs, and reputational protection. Adopt platforms like SAGA® that automate deep web and dark web monitoring, offering filtered, incident-ready intelligence while reducing analyst exposure to harmful content. Misconfigurations, weak authentication, or stale credentials can expose private content—leading to unauthorized access, data leakage, and compliance issues. A dark web marketplace is the equivalent of eBay but on the dark web. People use these platforms to sell illegal items, such as drugs, weapons, hacking services, stolen goods, and illegal services.
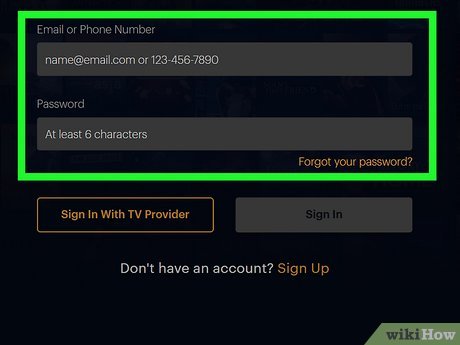
Log360 integrates with Constella Intelligence, the AI-driven identity intelligence provider, to continuously monitor dark web for security threats. By instantly alerting you to any PII exposure on the dark web, Log360’s monitoring capability reduces the risk of identity theft and data abuse for any gain, fraud, or extortion attempts. Multi-Factor Authentication (MFA) is an extra layer of security you can enable on your accounts. MFA protects you in the event that someone gains access to your login credentials since it requires a one or more methods of authentication before they’re able to successfully log in.

This data may include passwords, billing information, or purchase history—accessible to the user upon logging in but hidden from everyone else. Organizations of all sizes, even large enterprises, can regularly leak sensitive data via public GitHub repos. The platform represents an often overlooked vector for cybercriminal reconnaissance and initial access.
This visible portion includes all websites and resources that search engines can discover and index. It’s not easy to remove personal data from the Deep Web or Dark Web. Although most of this Deep Web can contain legitimate content that users can control with privacy settings and requests, much of the Dark Web contains data without the owners’ consent. People worrying about their data need to check their digital footprint periodically and seek services specifically offering data removal and monitoring services in order to minimize the potential risks. The deep web contains private networks used by business organizations, governmental departments, and educational institutions.



