The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Blockchain even has an HTTPS security certificate for even better protection. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki.
Recognize And Avoid Phishing Links

Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites.
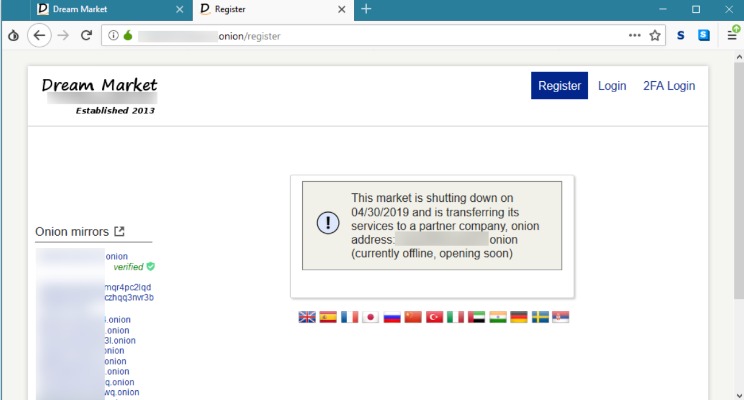
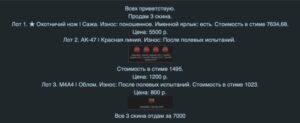
What Is A Darknet Market?
Private Internet Access even offers the Shadowsocks proxy for added security. There’s also MultiHop that boosts your encryption, along with MACE which blocks tracking. PIA doesn’t pull punches, so it strikes back against its competition with a proven-in-court no-logs policy, split tunneling, and even port forwarding to diversify its apps. While you can visit the obscure part of the internet without a VPN, it’s better to go with one.
Tools Needed For Safe Access
- While this may all sound sophisticated, it is a financial crime and very risky.
- Users contribute bandwidth and storage space, forming a cooperative network.
- Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users.
- We must explain that Tor is safe on paper but practice has shown that this browser can fail you.
This process is called “crawling,” where the crawlers follow links to different websites and index them for future reference. Being hidden doesn’t translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk. However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. To access those specific darknet networks, you will need to use the specific browsers developed for them. However, bear in mind that they are often less user-friendly than Tor (which makes accessing the dark web easy).
How To Access The Dark Web
Your connection also may be encrypted but if you do something like send an email from your personal account, then anyone with access to your inbox will know that you were online at that time. The best VPNs will anonymize your browsing by encrypting the connection between your device and the VPN provider. This makes it extremely difficult for your ISP or anyone with access to your internet records to know which sites you visit or apps you use. You can also find a few free VPN services, but be aware of the risks if you’re still using legacy VPNs in your organization. However, if we’re being honest, the majority of activity on darknet markets involves illegal or heavily regulated items. A 2020 study found that almost 57% of sites on the Tor network hosted some form of illegal content.
Tor Opens The Gateway To The Darknet
DuckDuckGo is built into the Tor browser, making it a convenient option for looking up dark web websites. However, before you start your search, toggle the button beside “Onionize” to anonymize your session. This hides your activity and personal identifiers so you can browse safely, protected from prying eyes and identity theft.
Watch Out; Your ISP Could See You Using The Tor
There’s a fascinating thread on Reddit (not remotely safe for work) where dark web users share their stories. Some of the tales are enough to make you tape over your webcam and disable your router just in case. Think of it as the dodgy bit of town where sensible people don’t go after dark. Since your connection is routed through multiple tor relays, page loading times can be very slow making effective searching extremely time-consuming. Not only is browsing via tor more secure, it also is more private as it effectively shuts out online trackers. The Tor browser is based on Firefox and makes use of extensions like ‘NoScript’ to prevent harmful code from loading and there’s a built-in ad blocker (see below).
Criminal Hacking Services
So, you should never share your personal information on the dark web. What’s more, they can also sell you personal information on the dark web as your personal data has a monetary value on the dark web. The dark web is a playground for hackers, cybercriminals, and people with nefarious objectives.
Users can create customizable profiles, have friends, and participate in forum discussions. Unlike the clear/surface web, where Google and safe search engines index all the relevant search results and present only the best to the users, the dark web doesn’t have that luxury. For this reason, users should be cautious when using their browsers. The dark web is a hidden part of the internet that can be accessed through limited resources. Moreover, you need to be more cautious while accessing it, as without proper safety, you can fall into the wrong hands and face serious consequences. Following are important tips you need to remember while visiting this dark part of the web.
While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is.
Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web. Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address.
What Is The Darknet? How The Web’s Secretive, Hidden Underbelly Works
The dark web itself is not illegal, but it’s largely connected with unscrupulous and illegal operations. That’s why it has such a foreboding and even dangerous reputation. It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data. We will be exploring the top 10 Dark Web markets in this article.
Its VPN Accelerator distributes the CPU load between multiple processes in OpenVPN, and modifies the servers’ Linux stacks to shorten the normal packet processing path. All Surfshark servers are RAM-only and support the WireGuard, IKEv2, and OpenVPN protocols. The company operates a strict no-logs policy and protects internet traffic using AES-256-GCM encryption together with a SHA512 authentication hash and 2048-bit DHE-RSA key exchange.
There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship.