If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous.
Install The Tor Browser
Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it. It describes itself as a tool for social change and “a project to create democratic alternatives.” Riseup requires you to have the onion link as well as an invitation.
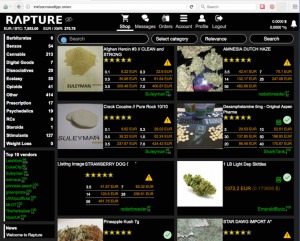
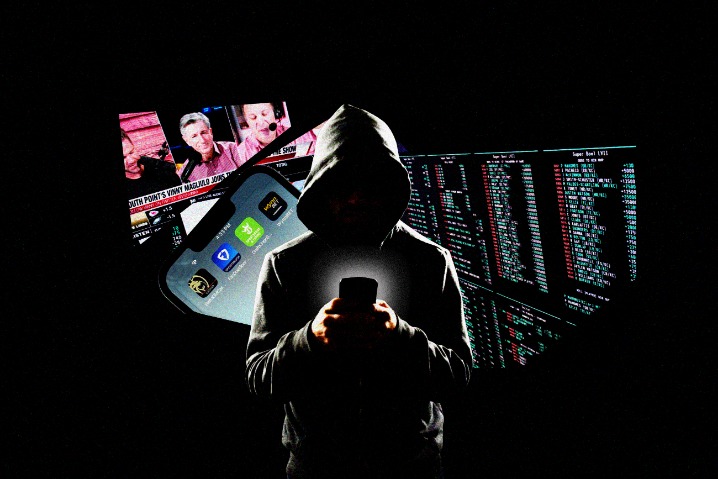
How Complex Are Dark Web Marketplaces Currently?
The marketplace extensively vets vendors listed within its deep web environment that offer a wide range of product portfolios, including security solutions, digital services, and specialized equipment. It stands as a reliable alternative to the defunct Alphabay Market as it continues to position itself as the premier source for advanced privacy-focused digital commerce. Awazon Market is a top-tier dark web marketplace with claims to revolutionize secure anonymous commerce.
Key Features Of Brandefense’s Dark Web Monitoring Solution
Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites.
Introduction: How Much Of The Internet Can You See?
It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
- Even people with zero technical knowledge can buy phishing kits, ransomware, or stolen logins.
- Law enforcement agencies actively monitor these markets and can track users despite anonymity measures.
- Once the buyer confirms satisfaction, the funds are released to the seller.
- Simply put, accessing and browsing the dark web is perfectly legal.
The Hidden Wiki & Co

Buyers can purchase a range of digital goods and services, which include illicit drugs, software and malware, and services related to fraud. The marketplace has over 8,400 listings and 500 vendors who communicate in English and accept Bitcoin for transactions. Darknet markets facilitate transactions for illegal goods and services.
How To Gain Safe Access To The Dark Web Marketplaces
Dark web monitoring can supplement other tools used to gather preemptive threat intelligence, such as the Mitre ATT&CK framework. In addition, the dark web can’t be accessed through typical browsers such as Firefox or Chrome. It can only be accessed through an encrypted peer-to-peer network connection or by using an overlay network, such as the Tor browser. The browser is free to download and use, and works with all major operating systems.
Just because the seller has good reviews does not mean you can trust them. There’s nothing stopping sellers from packing up and leaving the market at any time. They could get a batch of bad products, get arrested before they can ship your order, or any other number of things.
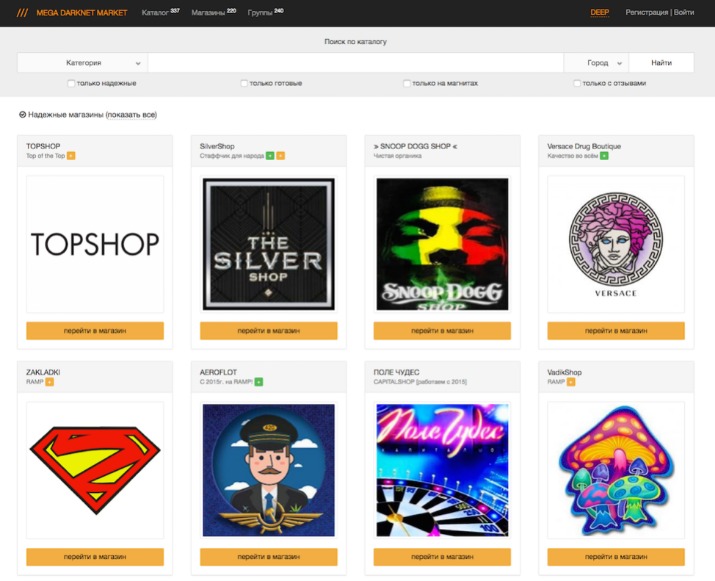
However, the dark web is so complex and vast that if law enforcement takes down one market, it pops up elsewhere. For instance, after the closure of Genesis Market, its website came back after a few weeks. If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding. What’s more concerning is that most of the time, we don’t know about these flaws, and by the time we try to fix them, we come to know it’s too late.
- See how our intelligent, autonomous cybersecurity platform harnesses the power of data and AI to protect your organization now and into the future.
- The only way in is through the use of special software that renders all users anonymous and untraceable.
- Therefore, it’s a no-brainer that businesses should implement dark web monitoring to identify data breaches, cyber risks, and several other illegal activities.
- These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
On average, the marketplace consists of more than 11,000 items and 1000 vendors. In April 2016, its APIs were compromised, resulting in stolen messages. But since its relaunch, the developers are focusing more on operational security and ensuring that users can have a good experience on this site. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities.
TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely.
Industries That Benefit The Most From Dark Web Monitoring 2025
Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is. Surprisingly, most guns on the darknet actually start as legal products.
Despite all the attacks, blocks, and the constant pressure from the authorities, the forum remains active. The forum is accessible through Tor and the surface web, and it’s available in English. Besides, LeakBase functions as a marketplace and as a discussion center where cybercriminals exchange compromised data. Moreover, it features a high number of stealer log data that includes credential pairs like passwords and email combinations. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today.
Please note that you must take great care when using the Dark Web as sites often contain adware, spyware, malicious links, and scams. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. The first step for any organization that wants a successful dark web forum monitoring is to start by establishing the goals, the areas to monitor, and the rules of engagement. Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of what they should look for to bolster the monitoring efforts.