Now that your connection is active, it’s encrypted and untraceable by your internet provider. Everything you do...
acess
The company operates a strict no-logs policy and protects internet traffic using AES-256-GCM encryption together with a...
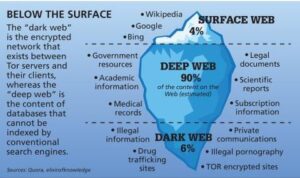
Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts...