
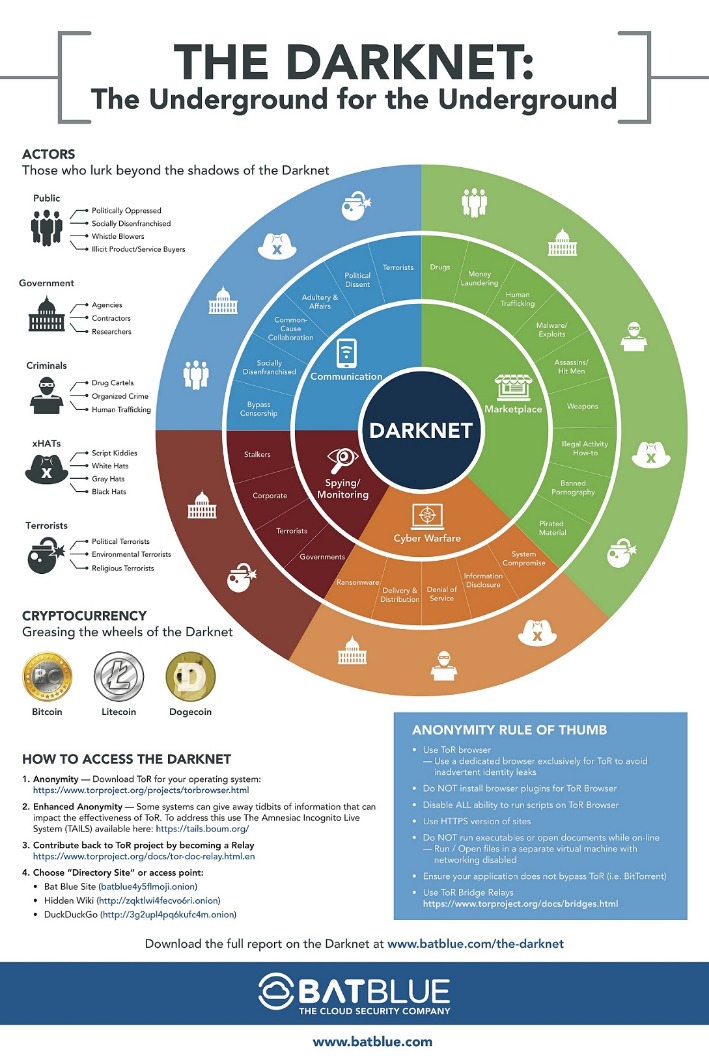
However, you can find some legal items in the darknet marketplace. Besides, not everyone wants to purchase an illegal item – some want items anonymously. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets. Due to being the most popular and the oldest coin, Bitcoin is traceable. However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets.
Efforts to host and index hidden sites flourished with platforms like DuckDuckGo and Not Evil, facilitating users in their pursuit of anonymity. When using Tor for enhanced privacy and anonymity, it’s crucial to consider the security of your email communications. While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing.
Dark Web Safety: How To Access The Darknet And Deep Web Securely
The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection. Always tread carefully whenever crowdsourcing information on how to navigate the dark web. Try LifeLock free for 30 days to receive notifications if we find your personal information on the dark web and help protect against identity theft.
Also, it should be common knowledge not to share personal information online. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web. The cost can be exorbitant, but for victims, it’s always higher and devastating. For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. Moreover, sensitive personal documents are made available on the dark web.
What Is The Onion Network?
- In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace.
- The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones.
- Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide.
- DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers.
- Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr…
It means that it can be overwhelming to get what you’re looking for, and as a result, it’s very easy to stumble into a place you could never want to be. Therefore, to ensure that you stay anonymous on the dark web, you can use Bitcoin mixers (also known as cryptocurrency tumblers) or opt for a privacy-focused coin such as Zcash and Monero. So, you should never forget to avoid using your credit and debit cards for purchases on the dark web. You should always use anonymous crypto wallets or stay away from dark webshops. Even if the seller accepts traditional payment means, you should always opt for crypto payments while transacting on the dark web.
Cybersecurity Best Practices For Protecting Your Digital Assets

Because traffic never leaves the Tor network, neither Internet service providers nor platform operators can easily trace the sender—crucial protection in sectors where retaliation is swift. In February 2011, Ross Ulbricht—using the alias “Dread Pirate Roberts”—opened Silk Road, the first modern darknet marketplace. Built on Tor and fueled by Bitcoin, the site let buyers and sellers trade drugs and contraband with unprecedented impunity until the FBI shuttered it in October 2013.
Official Onion Links:
This book makes the ambitious promise to protect readers from NSA spying by using Tor. Beyond the lessons about the dark web, the book explains all you need to know about the Tor network and an onion site. It further provides insights into what you stand to gain from Tor and similar dark web technologies.
Can A VPN And Tor Make The Dark Web Completely Private And Secure?
These services can potentially log your IP address or expose your information through various means, undermining the benefits Tor offers. As the digital environment evolves, so do the tactics employed by cybercriminals, law enforcement agencies, and privacy advocates. Staying safe and anonymous often means continuously educating yourself, adapting your methods, and refining your tools. Ultimately, the Dark Web is neither purely nefarious nor inherently virtuous—it’s a dynamic environment shaped by the motivations and actions of its users. Your decisions, responsible conduct, and awareness of potential risks will determine your experience in this hidden realm.
A Brief Overview & History Of Darknets & Dark Markets
They are not indexed by public search engines, and access requires knowing the specific address. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Accessing the Dark Web can expose you to a range of risks that might not be immediately apparent. While many visitors manage to browse hidden services without incident, staying safe requires constant vigilance.
Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. Still, even with these crackdowns and better defenses, dark web markets just keep coming back.

Alternative Anonymous Networks
With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. You can even find things such as BIN checkers and PayPal cookie converters.
It quickly outgrew its military roots, emerging as the Tor browser, a free gateway to the dark web’s digital back alleys. It is now one of the most widely used browsers to access the dark web. From information security threats like identity theft and malware to scams and surveillance, navigating the dark web without caution can lead to real dangers. So, is the dark web a lawless underworld or a misunderstood frontier for privacy and free expression? Accessing darknet requires using Tor Browser, a special web browser that routes your internet traffic through a global network of relays managed by volunteers.
Some things, like medical records, driver’s licenses, and passport information. The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of. In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone. Often shrouded in mystery and portrayed negatively, the dark web can be daunting for any beginner to navigate. However, with the right knowledge and guidance, you can safely explore what lies in the hidden corners of the Internet.



